Recently, I’ve reduced my hours working at the Bodleian in order to be able to spend more time working on Three Rings and engaging in other bits of freelance work… and to increase my flexibility so that I can be available for childcare and to generally make things more-convenient for the other Greendalians and I. Unfortunately, on my very second day of this new working arrangement Nena (which I built in 2008) had her power supply blow up, which sort-of threw a spanner into the works. This, along with a scary recent hard drive failure in JTA‘s computer, I took as being a sign from the Universe that it was time to build myself a new PC to replace Toni, my primary box, and relegate Toni to be the new Nena. It was time to build: Cosmo.
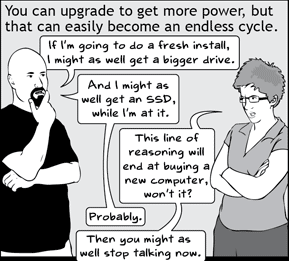
Given that I had a little cash to burn, I decided that it must finally be time to fulfil a couple of long-standing dreams I’ve had – things I’ve wanted to do when building my last two or three computers, but never been able to justify the expense. And so I set out to build my new “dream computer”: a beast of a machine which would present me with some fresh engineering challenges during construction. Key features that I wanted to include were:
Liquid cooling
Most computers are air-cooled: the “hot” components like the processor and graphics chipset are covered with a heatsink (which works just like the fins on a motorcycle engine: drawing heat away through contact with cool air) and, generally, a fan (to improve airflow over the heatsink and thus increase cooling). Air cooling, though, is inefficient (the transfer of heat from components to air isn’t very fast) and noisy (“hot”-running air-cooled computers are annoyingly loud), and so in my last few PC builds I’ve drifted towards using cooler and quieter components, such as processors that are overpowered for what they’ll actually be asked to do (like Tiffany2, who’s virtually silent) and all-in-one liquid coolers for my CPUs (like these ones, from CoolerMaster – note that these still have a fan, but the use of a radiator means that the fan can be large, slow, and quiet, unlike conventional CPU fans which spin quickly and make noise).

But I’ve always had this dream that I’d one day build a true, complete, custom water-cooled system: taking a pump and a reservoir and a radiator and cutting pipe to fit it all around the “hot” components in my case. The pumps and fans of water-cooled systems make them marginally louder than the quietest of fan-driven, air-cooled computers… but are far more efficient, drawing a massive amount of heat away from the components and therefore making it possible to pack more-powerful components closer together and overclock them to speeds undreamed of by their manufacturers. A liquid cooling solution was clearly going to be on the list.
Multi-GPU
And how to best make use of that massive cooling potential? By putting an extra graphics card in! The demands of modern 3D games mean that if you want to run at the highest resolutions, quality settings, and frame rates, you need a high-end graphics card. And if you want to go further still (personally: I love to be able to run Bioshock Infinite, Far Cry 3, or Call Of Duty: Ghosts at a massive “ultra-widescreen”, wrap-around resolution of 5760×1080 – that’s triple the number of pixels found on your 1080p HDTV), well: you’re going to want several high-end graphics cards.

Both ATI/AMD’s Radeon and Nvidia’s GeForce series’ of chipsets are capable of running in tandem, triple, or quadruple configurations (so long as your motherboard and power supply hold up, and assuming that you’ve got the means to keep them all cool, of course!), and as a result all of my last few PC builds have deliberately been “ready” for me to add a second graphics card, down the line, if I decided I needed some extra “oomph” (instead, I’ve always ended up with a new computer by that point, instead), but this would be the first time I’d actually design the computer to be multi-GPU from the outset.
SSD/RAID 1+0 Combo
Toni featured a combination of a solid-state drive (flash memory, like you get in pendrives, but faster) instead of a conventional hard drive, to boot from, and a pair of 2TB “traditional” hard drives, all connected through the perfectly-adequate SATA 2 interface. Using an SSD for the operating system meant that the machine booted up ludicrously quickly, and this was something I wanted to maintain, so clearly the next step was a larger, faster, SATA 3 SSD for Cosmo.
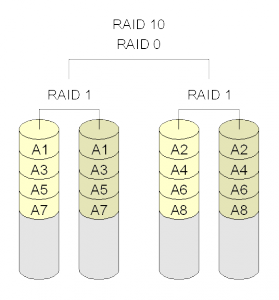
Anybody who’s messed about with computer hardware for as long as I have has seen a hard drive break down at least once, and JTA’s recent malfunction of that type reminded me that even with good backups, the downtime resulting from such a component fault is pretty frustrating. This, plus the desire to squeeze as much speed as possible out of conventional hard drives, made me opt for a RAID 1+0 (or “RAID 10”). I’d tie together four 2TB hard drives to act as a single 4TB disk, providing a dramatic boost in redundancy (one, or possbily even two drives can be completely destroyed without any data loss) and speed (reading data that’s duplicated across two disks is faster because the computer can be effectively “reading ahead” with the other disk; and writing data to multiple disks is no slower because the drives work at the same time).
A few other bits of awesome
Over my last few PC builds, I’ve acquired a taste for a handful of nice-to-have’s which are gradually becoming luxuries I can’t do without. My first screwless case was Duality, back in the early 2000s, and I’d forgotten how much easier it was to simply clip hard drives to rails until I built Nena years later into a cheap case that just wasn’t the same thing.

Another thing I’ve come to love and wonder how I ever did without is modular power supplies. Instead of having a box with a huge bundle of cables sticking out of it, these are just a box… the cables come separately, and you only use the ones you need, which takes up a lot less space in your case and makes the whole process a lot tidier. How did it take us so long to invent these things?
Needless to say, the planning about building Cosmo was the easy and stress-free bit. I shall tell you about the exciting time I had actually putting her together – and the lessons learned! – later. Watch this space, and all that!






![Cash machine: "Do you wish to carry out a Get Cash or Emergency Cash transaction? [No] [Yes]" Cash machine: "Do you wish to carry out a Get Cash or Emergency Cash transaction? [No] [Yes]"](https://bcdn.danq.me/_q23u/2012/06/IMG_5833-300x200.jpg)