Well into the afternoon and the party is still on.
Blog
A poem about Silicon Valley, assembled from Quora questions about Silicon Valley
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Why do so many startups fail?
Why are all the hosts on CouchSurfing male?
Are we going to be tweeting for the rest of our lives?
Why do Silicon Valley billionaires choose average-looking wives?What makes a startup ecosystem thrive?
What do people plan to do once they’re over 35?
Is an income of $160K enough to survive?
What kind of car does Mark Zuckerberg drive?…
May Day morning in Oxford, 2019
09:20 and the revellers – most of whom have been partying all night – are still at it outside the Clarendon Building on Broad Street.
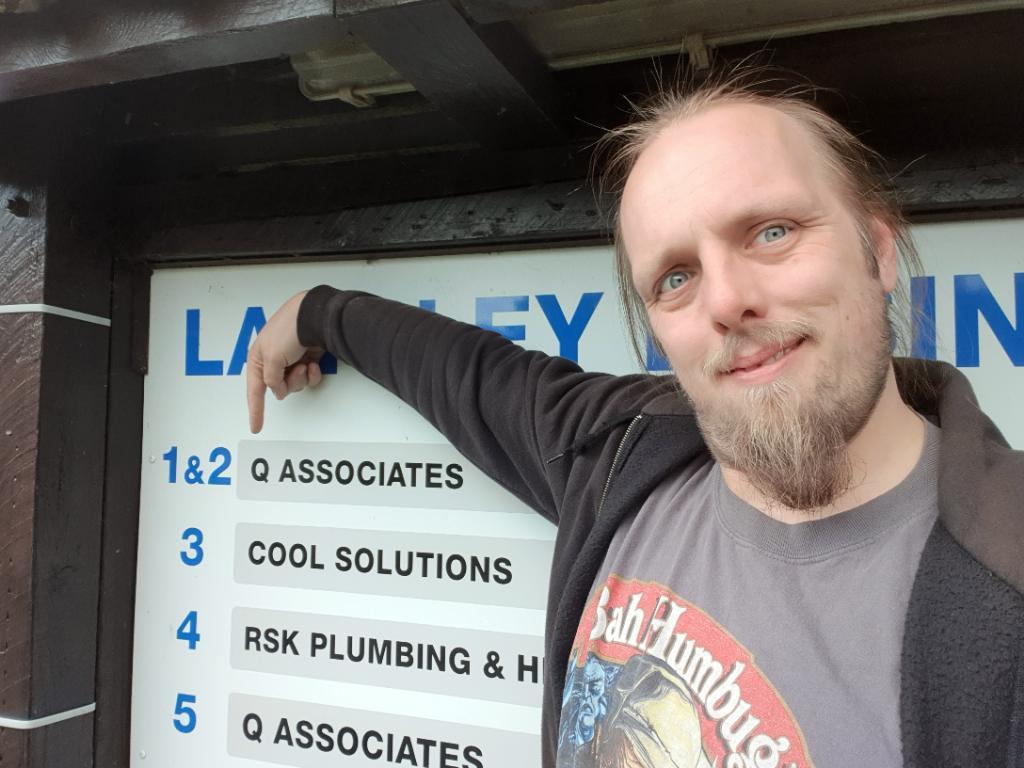
Dan Q found GC48ZDW The End Of The World is Nigh
This checkin to GC48ZDW The End Of The World is Nigh reflects a geocaching.com log entry. See more of Dan's cache logs.
Quick cache and dash while in the vicinity. Overshot the obvious parking place and so parked up the road at the premises of “Q Associates”. Figured they wouldn’t mind given than it’s Sunday. Plus their company has the same name as my surname, so I could probably claim it’s mine if anybody challenged me. Cool solution!
Dan Q found GC6DD4G 10MG TABLETS
This checkin to GC6DD4G 10MG TABLETS reflects a geocaching.com log entry. See more of Dan's cache logs.
Easy find once I’d looked at the hint. Container very exposed; re-hid. Excellent log book, highly thematic! Thanks for showing me this spot.
What can board game strategy tell us about the future of the car wash?
I’m increasingly convinced that Friedemann Friese‘s 2009 board game Power Grid: Factory Manager (BoardGameGeek) presents gamers with a highly-digestible model of the energy economy in a capitalist society. In Factory Manager, players aim to financially-optimise a factory over time, growing production and delivery capacity through upgrades in workflow, space, energy, and staff efficiency. An essential driving factor in the game is that energy costs will rise sharply throughout. Although it’s not always clear in advance when or by how much, this increase in the cost of energy is always at the forefront of the savvy player’s mind as it’s one of the biggest factors that will ultimately impact their profit.
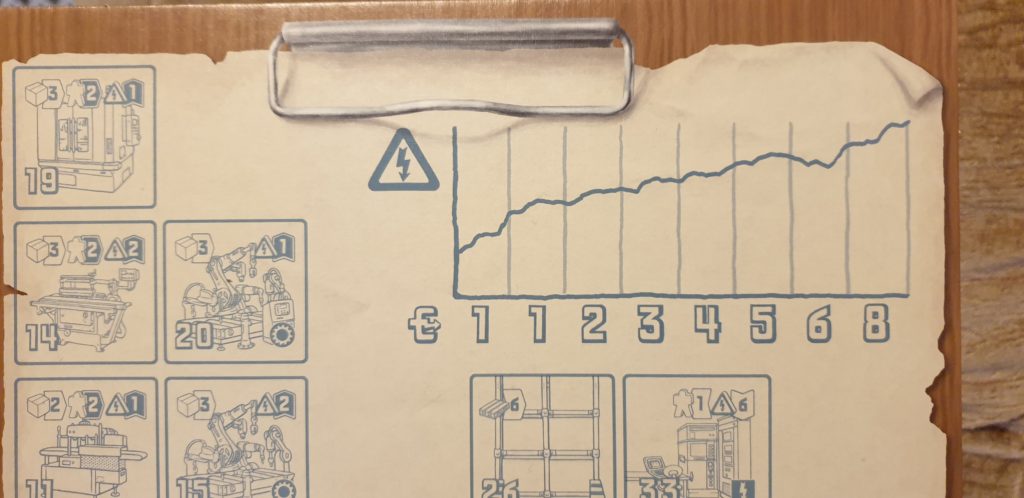
Given that players aim to optimise for turnover towards the end of the game (and as a secondary goal, for the tie-breaker: at a specific point five rounds after the game begins) and not for business sustainability, the game perhaps-accidentally reasonably-well represents the idea of “flipping” a business for a profit. Like many business-themed games, it favours capitalism… which makes sense – money is an obvious and quantifiable way to keep score in a board game! – but it still bears repeating.
There’s one further mechanic in Factory Manager that needs to be understood: a player’s ability to control the order in which they take their turn and their capacity to participate in the equipment auctions that take place at the start of each round is determined by their manpower-efficiency in the previous round. That is: a player who operates a highly-automated factory running on a skeleton staff benefits from being in the strongest position for determining turn order and auctions in their next turn.
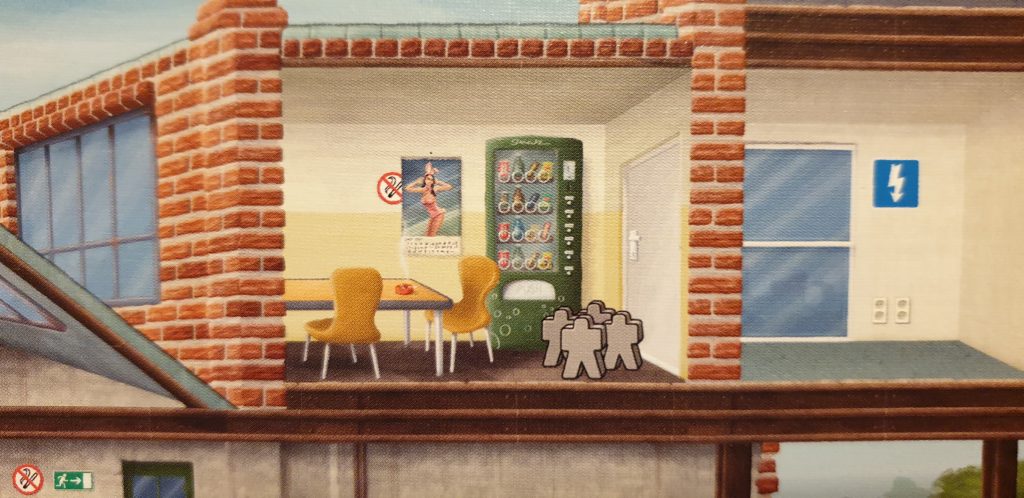
The combination of these rules leads to an interesting twist: in the final turn – when energy costs are at their highest and there’s no benefit to holding-back staff to monopolise the auction phase in the nonexistent subsequent turn – it often makes most sense strategically to play what I call the “sweatshop strategy”. The player switches off the automated production lines to save on the electricity bill, drags in all the seasonal workers they can muster, dusts off the old manpower-inefficient machines mouldering in the basement, and gets their army of workers cranking out widgets!
With indefinitely-increasing energy prices and functionally-flat staff costs, the rules of the game would always eventually reach the point at which it is most cost-effective
to switch to slave cheap labour rather than robots. but Factory Manager‘s fixed-duration means that this point often comes for all players in many games at the same
predictable point: a tipping point at which the free market backslides from automation to human labour to keep itself alive.
There are parallels in the real world. Earlier this month, Tim Watkins wrote:
The demise of the automated car wash may seem trivial next to these former triumphs of homo technologicus but it sits on the same continuum. It is just one of a gathering list of technologies that we used to be able to use, but can no longer express (through market or state spending) a purpose for. More worrying, however, is the direction in which we are willingly going in our collective decision to move from complexity to simplicity. The demise of the automated car wash has not followed a return to the practice of people washing their own cars (or paying the neighbours’ kid to do it). Instead we have more or less happily accepted serfdom (the use of debt and blackmail to force people to work) and slavery (the use of physical harm) as a reasonable means of keeping the cost of cleaning cars to a minimum (similar practices are also keeping the cost of food down in the UK). This, too, is precisely what is expected when the surplus energy available to us declines.
I love Factory Manager, but after reading Watkins’ article, it’ll probably feel a little different to play it, now. It’s like that moment when, while reading the rules, I first poured out the pieces of Puerto Rico. Looking through them, I thought for a moment about what the “colonist” pieces – little brown wooden circles brought to players’ plantations on ships in a volume commensurate with the commercial demand for manpower – represented. And that realisation adds an extra message to the game.
Beneath its (fabulous) gameplay, Factory Manager carries a deeper meaning encouraging the possibility of a discussion about capitalism, environmentalism, energy, and sustainability. And as our society falters in its ability to fulfil the techno-utopian dream, that’s perhaps a discussion we need to be having.

But for now, go watch Sorry to Bother You, where you’ll find further parallels… and at least you’ll get to laugh as you do so.
Guess that sex act #CONTENT
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
My 12th favourite and my 27th favourite YouTubers just did a collaboration and it’s brilliant. Also: I totally knew seven out of the twelve terms Dr Doe brought to the table and would have been able to guess at least one more (as well as, of course, knowing what TomSka meant by his British slang), so this video made me feel clever.
Lyme Regis To Limekilns: A 500-Mile Lime-E Adventure Across The UK
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
It all started out as a joke.
Last year, Robin Varley and his friend Sergio thought it would be an amusing challenge to pedal the 50-odd mile gap between Brixton and Brighton using only London’s colloquially-named Boris Bikes. The trip lasted just over 10 hours, including a brief photo op with Gatwick police, and set the pair back a modest sum of 40 GBP.
This year Robin enlisted the help of fellow adventure-seeker Magnus Mulvany, and while the duo kept the alliterative theme of the campaign they opted for a significantly more daunting circuit.
…
You heard about it here first, probably, but here’s Lime Bikes’ write-up of Robin and Magnus’s adventure.
Towards an Information Operations Kill Chain
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Cyberattacks don’t magically happen; they involve a series of steps. And far from being helpless, defenders can disrupt the attack at any of those steps. This framing has led to something called the “cybersecurity kill chain”: a way of thinking about cyber defense in terms of disrupting the attacker’s process. On a similar note, it’s…
Bruce proposes a model to apply the cybersecurity kill chain to the problem of thwarting information operations of the types that we’re seeing day-to-day in the cyberwar landscape. Or at least, to understand it. Interesting reading, but – and call me cynical – I don’t know if it’s possible to implement some of the kill-stops that would be required to produce a meaningful barrier.
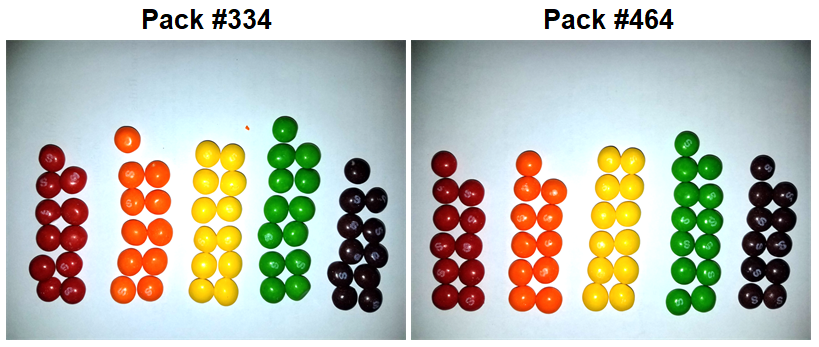
Follow-up: I found two identical packs of Skittles, among 468 packs with a total of 27,740 Skittles
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Applied mathematics at its… best? After predicting statistically that it would take 400-500 packets of Skittles before you’d expect to find the same permutation of colours, an experiment finds empirical backing for this answer at pack number 464.
Somebody get the Ig Nobel Prize folks on the line.
Dan Q enabled GC86MHH Top of the Footpath
This checkin to GC86MHH Top of the Footpath reflects a geocaching.com log entry. See more of Dan's cache logs.
Turns out the glue I’d used had interacted badly with the material: wasn’t melting because of the heat (although that won’t have helped) but because of a chemical reaction on the plastic! Repaired and replaced, all good to go now!
Dan Q temporarily disabled GC86MHH Top of the Footpath
This checkin to GC86MHH Top of the Footpath reflects a geocaching.com log entry. See more of Dan's cache logs.
Wow, this cache container really HAS been damaged by the hot weather. Removed for repair, back this weekend hopefully!
Why do people choose frameworks over vanilla JS?
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
This week on Twitter, Maxime Euzière asked why people choose large frameworks over vanilla JS. There are quite a few reasons. Some of them are really valid. Many of them aren’t. Here are the ones I see most often (with commentary). Vanilla JS is harder. No, it’s often not. Modern vanilla JS has taken many…
Like many people who were already developing for the Web when Javascript first reared its (ugly) head, I would later be delighted when libraries like Prototype and later jQuery would arrive and start doing the “heavy lifting” for me. Not having to do DOM parsing or (especially) Ajax the “long way” (which was particularly long given the workarounds that needed to be done for cross-compatibility) was a huge boon and made it possible for me to write applications that I wouldn’t otherwise have been able to.
But in recent years, I’ve really been enjoying “vanilla” JS. As a language, JavaScript has really grown-up lately, and with modern (and evergreen) browsers dominating the landscape, everybody benefits from these new features relatively soon after they become available. Of course, it’s still important to see any JavaScript as a progressive enhancement that not everybody will experience, but it’s still true, now, that the traditional barriers to writing excellent code in the language are rapidly evaporating.
I no longer add jQuery to a project as a matter of course (and in fact I think it’s been over a year since I deliberately added it to a new project), and that’s great.
Escape Room [NSFW]
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Regular readers will know already that I’ve been a huge fan of comic author Tailsteak, ever since Ruth, many years ago, introduced me to his work. I’m particularly enjoying Forward, his latest webcomic: so much so that in an effort to work around its lack of an RSS feed I accidentally stole unpublished work from him earlier this year (oops!).
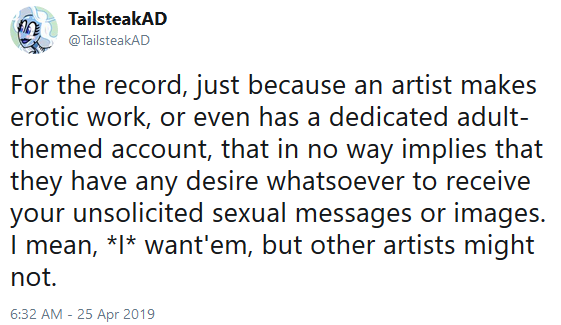
He announced yesterday his new secondary Twitter account, @TailsteakAD (the “AD” is for “After Dark”) and was delighted from the very top tweet onwards:
Anyway: a short while later I found a 20-page comic he’d made called The Escape Room: read it on Twitter or via Threadreader. It might be exactly the comic you’ve always been looking for, assuming that the comic you’ve always been looking for combines B/D, gay sex, and escape room puzzle mechanics. NSFW, obviously.
Suddenly I feel like the escape rooms I go to aren’t quite as good as I thought.
Dan Q performed maintenance for GC1G4E3 Kinkering Congs Their Titles Take
This checkin to GC1G4E3 Kinkering Congs Their Titles Take reflects a geocaching.com log entry. See more of Dan's cache logs.
Added more-waterproof cache container. Improved clue. Note that old cache container may still be in place: wasn’t able to find it and was being watched by muggles; I’ll return to re-hunt for and remove the old container soon.