This checkin to GC9PMF7 Crossing the street reflects a geocaching.com log entry. See more of Dan's cache logs.
QEF while on the way down from Taoro Park with Ruth. SL, TFTC!
This checkin to GC9PMF7 Crossing the street reflects a geocaching.com log entry. See more of Dan's cache logs.
QEF while on the way down from Taoro Park with Ruth. SL, TFTC!
This checkin to GC1PYFN Parque Taoro reflects a geocaching.com log entry. See more of Dan's cache logs.
Ruth and I made several attempts today without success: a muggle was sat nearby in such a way that access to the GZ was obstructed. We took a walk to the nearby Anglican church – whose architecture, if you ignore the volcanic rock, is uncannily like that of Anglican churches in the UK – but then we returned the muggle had very much set up camp and was going nowhere. We attempted to find a way to the cache from the opposite side without luck, and eventually had to give up. 😔
This checkin to GC9MCDM The Queen Of Mystery reflects a geocaching.com log entry. See more of Dan's cache logs.
After solving the riddle yesterday, my partner Ruth and I came up from the seafront to find this cache today. What a delightful spot to hide the cache, and what a wonderful puzzle (and spot of local literary history) with which to bring us here.
SL, FP awarded. Greetings from Oxfordshire, UK. TFTC!
In January 2024 I participated in Bloganuary, a “write a blog post every day for a month” challenge organised by Automattic. I wasn’t 100% impressed by the prompts made available and was – as an employee of Automattic – shuffling towards trying to help make them better in a future year. To be part of the solution!
I didn’t participate in January 2025, because I was on sabbatical and – as well as it feeling a little “close” to work! – Bloganuary intersected with a winter-sun trip to Trinidad & Tobago, where – despite a state of emergency being declared – Ruth and I unlocked a geohashing graticule, experienced small-world serendipity, and generally explored beautiful and remote places.1

Of course, two significant things changed since then:
Ah well, I figured. I’d just do my own thing. I can write something for every day in January 2026, can’t I?
Generating a chart...
If this message doesn't go away, the JavaScript that makes this magic work probably isn't doing its job right: please tell Dan so he can fix it.
Turns out that yes, I can. 53 posts over 31 consecutive days, so far this year. This year might be my fastest run at 100 Days To Offload yet.
In general, I suppose I’ve been blogging more-frequently lately. Why is that? I guess it’s been a realisation that a blog post doesn’t always have to be polished to perfection. I still write long-form posts which require research and planning, like setting up a network of Windows 3.x VMs just to get screenshots of what programming then looked like or making that podcast episode with the music in it… but I’m also feeling more-free to just express myself in the moment. To share things I see that look interesting or funny or pretty, or just whatever I’m thinking. I’ve been using “kinds” to categorise my posts so it’s easy for people to avoid my more-inane stuff if they like, but that’s a secondary consideration because ultimately… I blog for me.
I’ve also been trying to make blogging more social. Over the last year I’ve made an effort to (visibly) “follow” more personal bloggers and correspond with them (including in new – by which I mean old – ways like exchanging postcards!).
Anyway… all of which is to say that I’ve been writing more and I’ve been loving it. The best way to read more of what I’m writing, if you’d like to, remains: by subscribing via RSS.
But regardless of how and why you’ve come to find this post – thanks for dropping be: drop me a message and say hi and let’s be friends.
1 I’d anticipated having a lack of Internet access, but in fact 4G was widespread throughout both islands and overall I managed to post something on every day except three in January 2025.
2 Based on friends I’ve spoken to, there seem to have been a lot more folks let go since; the company seems to be shrinking quite a lot, which might go some way to explaining my second observation too.
This checkin to GC9PVXZ EL CRÁTER DE LA RAMBLETA reflects a geocaching.com log entry. See more of Dan's cache logs.
My partner Ruth and I were disappointed not to be able to hike any of the trails up here today – they’re all closed – but enjoyed finding both the nearby Virtual and this Earthcache geocaches. The evidence of lava flows (that remain to this day!) are really quite impressive.
This checkin to GC9P71A El tEidE reflects a geocaching.com log entry. See more of Dan's cache logs.
My partner Ruth and I are spending a long weekend in Puerto de la Cruz. We loved coming up to see this beautiful, bleak, stark volcanic landscape.
TFTC!
If I’m on holiday and a hotel offers me eggs benedict for breakfast, I’ll almost always order it. But I’d never make it at home.
I tell myself that this is because hollandaise sauce is notoriously easy to mess up. That I don’t want to go through the learning process only to make something inferior to what I eat as a holiday treat.
But maybe it’s just that my brain wants to keep eggs benedict as a signifier that I’m on holiday. That I can unplug from the world, stop thinking about work, and enjoy a leisurely breakfast with some creamy eggs and a long black coffee.
Maybe eggs benedict just has to remain “holiday food”, for me.
RSS readers rock. Having a single place you connect for a low-bandwidth bundle of everything you might want to read means it doesn’t matter how slow the WiFi is on your aeroplane, you can get all the text content in one tap.
(I’m using Capy Reader to connect to FreshRSS, by the way.)
Time to catch up on some news, blogs, etc.!
It’s been said that when faced with a new piece of technology, a normal person asks “what does it do?”, but a hacker asks “what can I make it do?”.
This kind of curiosity is integral to a hacker mindset.
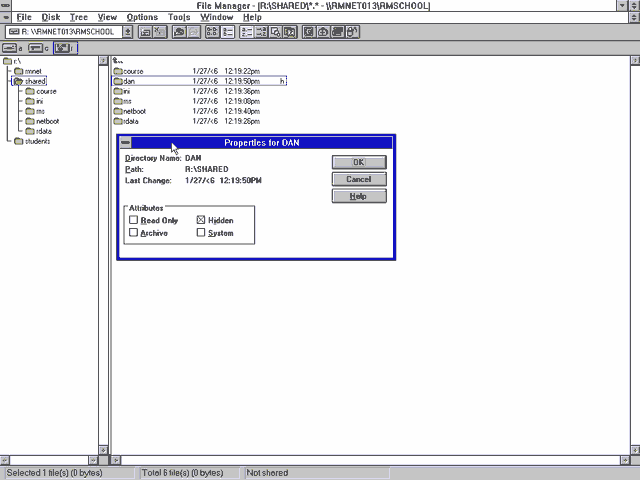
I can trace my hacker roots back further than my first experience of using an RM Nimbus M-Series in circa 19922. But there was something particular about my experience of this popular piece of British edutech kit which provided me with a seminal experience that shaped my “hacker identity”. And it’s that experience about which I’d like to tell you:
Shortly after I started secondary school, they managed to upgrade their computer lab from a handful of Nimbus PC-186s to a fancy new network of M-Series PC-386s. The school were clearly very proud of this cutting-edge new acquisition, and we watched the teachers lay out the manuals and worksheets which smelled fresh and new and didn’t yet have their corners frayed nor their covers daubed in graffiti.
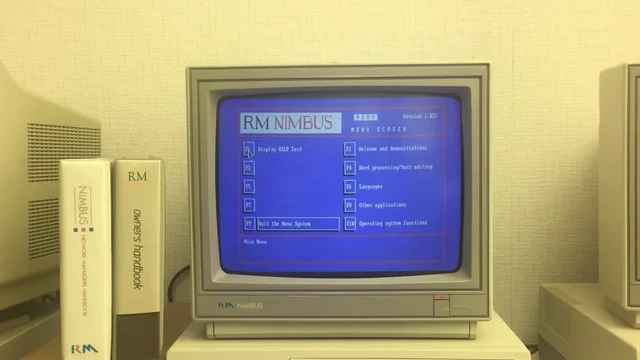
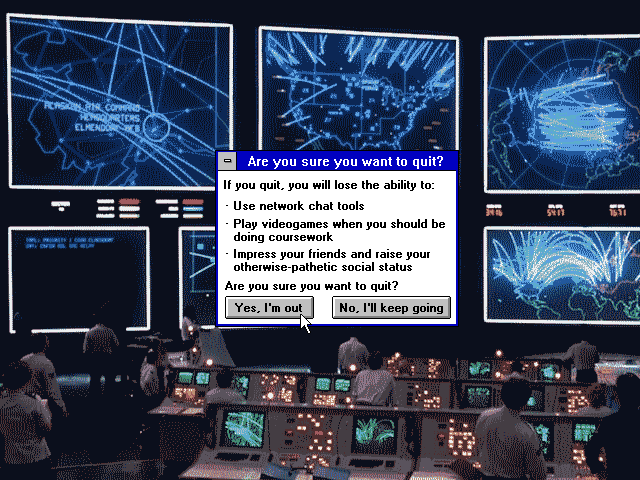
The new ones ran Windows 3 (how fancy!). Well… kind-of. They’d been patched with a carefully-modified copy of Program Manager that imposed a variety of limitations. For example, they had removed the File > Run… menu item, along with an icon for File Manager, in order to restrict access to only the applications approved by the network administrator.
A special program was made available to copy files between floppy disks and the user’s network home directory. This allowed a student to take their work home with them if they wanted. The copying application – whose interface was vastly inferior to File Manager‘s – was limited to only copying files with extensions in its allowlist. This meant that (given that no tool was available that could rename files) the network was protected from anybody introducing any illicit file types.
Bring a .doc on a floppy? You can copy it to your home directory. Bring a .exe? You can’t even see it.
To young-teen-Dan, this felt like a challenge. What I had in front of me was a general-purpose computer with a limited selection of software but a floppy drive through which media could be introduced. What could I make it do?
Spoiler: eventually I ended up being able to execute pretty much anything I wanted, but we’ll get to that. The journey is the important part of the story. I didn’t start by asking “can I trick this locked-down computer lab into letting my friends and I play Doom deathmatches on it?” I started by asking “what can I make it do?”; everything else built up over time.
I started by playing with macros. Windows used to come with a tool called Recorder,3 which you could use to “record” your mouse clicks and keypresses and play them back.
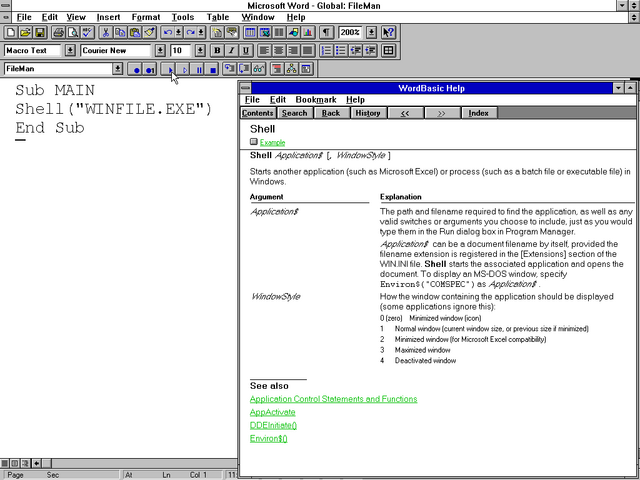
Then I noticed that Microsoft Word also had a macro recorder, but this one was scriptable using a programming language called WordBasic (a predecessor to Visual Basic for Applications). So I pulled up the help and started exploring what it could do.
And as soon as I discovered the Shell function, I realised that
the limitations that were being enforced on the network could be completely sidestepped.
Now that I could run any program I liked, I started poking the edges of what was possible.
I didn’t have a proper LAN at home7 So I really enjoyed the opportunity to explore, unfettered, what I could get up to with Windows’ network stack.
I started to explore the resources on the network. Each pupil had their own networked storage space, but couldn’t access one another’s. But among the directories shared between all students, I found a directory to which I had read-write access.
I created myself a subdirectory and set the hidden bit on it, and started dumping into it things that I wanted to keep on the network8.
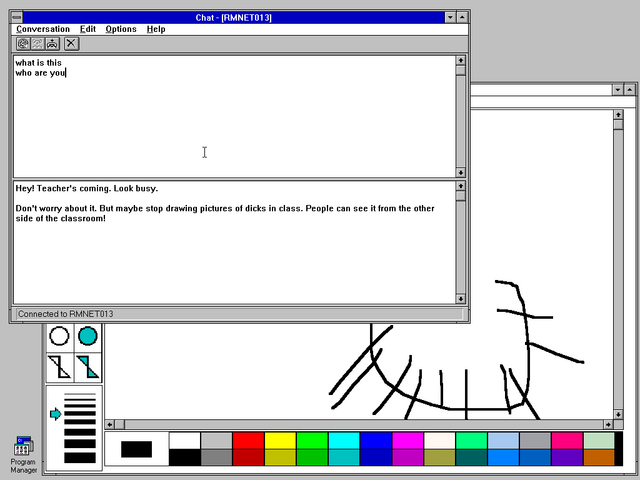
By now my classmates were interested in what I was achieving, and I wanted in the benefits of my success. So I went back to Word and made a document template that looked superficially like a piece of coursework, but which contained macro code that would connect to the shared network drive and allow the user to select from a series of programs that they’d like to run.
Gradually, compressed over a series of floppy disks, I brought in a handful of games: Commander Keen, Prince of Persia, Wing Commander, Civilization, Wolfenstein 3D, even Dune II. I got increasingly proficient at modding games to strip out unnecessary content, e.g. the sound and music files9, minimising the number of floppy disks I needed to ZIP (or ARJ!) content to before smuggling it in via my shirt pocket, always sure not to be carrying so many floppies that it’d look suspicious.
In a particularly bold move, I implemented a simulated login screen which wrote the entered credentials into the shared space before crashing the computer. I left it running, unattended, on computers that I thought most-likely to be used by school staff, and eventually bagged myself the network administrator’s password. I only used it twice: the first time, to validate my hypothesis about the access levels it granted; the second, right before I finished school, to confirm my suspicion that it wouldn’t have been changed during my entire time there10.
My single biggest mistake was sharing my new-found power with my classmates. When I made that Word template that let others run the software I’d introduced to the network, the game changed.
When it was just me, asking the question what can I make it do?, everything was fun and exciting.
But now half a dozen other teens were nagging me and asking “can you make it do X?”
This wasn’t exploration. This wasn’t innovation. This wasn’t using my curiosity to push at the edges of a system and its restrictions! I didn’t want to find the exploitable boundaries of computer systems so I could help make it easier for other people to do so… no: I wanted the challenge of finding more (and weirder) exploits!
I wanted out. But I didn’t want to say to my friends that I didn’t want to do something “for” them any more11.
I figured: I needed to get “caught”.
I chose… to get sloppy.
I took a copy of some of the software that I’d put onto the shared network drive and put it in my own home directory, this time un-hidden. Clearly our teacher was already suspicious and investigating, because within a few days, this was all that was needed for me to get caught and disciplined13.
I was disappointed not to be asked how I did it, because I was sufficiently proud of my approach that I’d hoped to be able to brag about it to somebody who’d understand… but I guess our teacher just wanted to brush it under the carpet and move on.
The school’s IT admin certainly never worked-out the true scope of my work. My “hidden” files remained undiscovered, and my friends were able to continue to use my special Word template to play games that I’d introduced to the network14. I checked, and the hidden files were still there when I graduated.
The warning worked: I kept my nose clean in computing classes for the remainder of secondary school. But I would’ve been happy to, anyway: I already felt like I’d “solved” the challenge of turning the school computer network to my interests and by now I’d moved on to other things… learning how to reverse-engineer phone networks… and credit card processors… and copy-protection systems. Oh, the stories I could tell15.
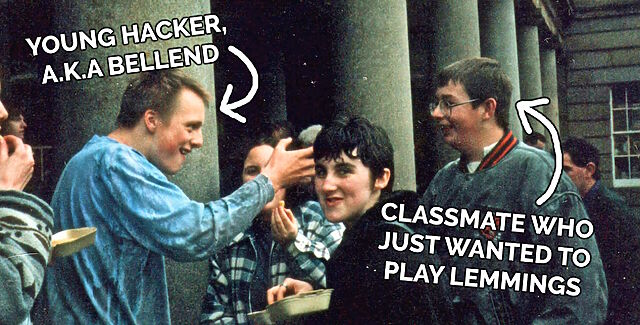
But I’ll tell you what: 13-ish year-old me ought to be grateful to the RM Nimbus network at my school for providing an interesting system about which my developing “hacker brain” could ask: what can I make it do?
Which remains one of the most useful questions with which to foster a hacker mentality.
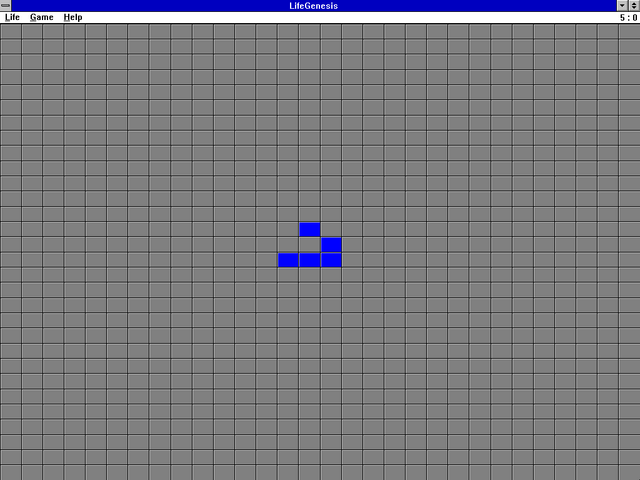
1 I first played Game of Life on an Amstrad CPC464, or possibly a PC1512.
2 What is the earliest experience to which I can credit my “hacker mindset”? Tron and WarGames might have played a part, as might have the “hacking” sequence in Ferris Bueller’s Day Off. And there was the videogame Hacker and its sequel (it’s funny to see their influence in modern games). Teaching myself to program so that I could make text-based adventures was another. Dissecting countless obfuscated systems to see how they worked… that’s yet another one: something I did perhaps initially to cheat at games by poking their memory addresses or hexediting their save games… before I moved onto reverse-engineering copy protection systems and working out how they could be circumvented… and then later still when I began building hardware that made it possible for me to run interesting experiments on telephone networks.
Any of all of these datapoints, which took place over a decade, could be interpreted as “the moment” that I became a hacker! But they’re not the ones I’m talking about today. Today… is the story of the RM Nimbus.
3 Whatever happened to Recorder? After it disappeared in Windows 95 I occasionally had occasion to think to myself “hey, this would be easier if I could just have the computer watch me and copy what I do a few times.” But it was not to be: Microsoft decided that this level of easy automation wasn’t for everyday folks. Strangely, it wasn’t long after Microsoft dropped macro recording as a standard OS feature that Apple decided that MacOS did need a feature like this. Clearly it’s still got value as a concept!
4 Just to clarify: I put more effort in to making animations, which were not part of my schoolwork back when I was a kid. I certainly didn’t put more effort into my education.
5 The computers had been configured to make DOS access challenging: a boot menu let you select between DOS and Windows, but both were effectively nerfed. Booting into DOS loaded an RM-provided menu that couldn’t be killed; the MS-DOS prompt icon was absent from Program Manager and quitting Windows triggered an immediate shutdown.
6 My secondary school didn’t get Internet access during the time I was enrolled there. I was recently trying to explain to one of my kids the difference between “being on a network” and “having Internet access”, and how often I found myself on a network that wasn’t internetworked, back in the day. I fear they didn’t get it.
7 I was in the habit of occasionally hooking up PCs together with null modem cables, but only much later on would I end up acquiring sufficient “thinnet” 10BASE2 kit that I could throw together a network for a LAN party.
8 Initially I was looking to sidestep the space limitation enforcement on my “home” directory, and also to put the illicit software I was bringing in somewhere that could not be trivially-easily traced back to me! But later on this “shared” directory became the repository from which I’d distribute software to my friends, too.
9 The school computer didn’t have soundcards and nobody would have wanted PC speakers beeping away in the classroom while they were trying to play a clandestine videogame anyway.
10 The admin password was concepts. For at least four years.
11 Please remember that at this point I was a young teenager and so was pretty well over-fixated on what my peers thought of me! A big part of the persona I presented was of somebody who didn’t care what others thought of him, I’m sure, but a mask that doesn’t look like a mask… is still a mask. But yeah: I had a shortage of self-confidence and didn’t feel able to say no.
12 Art is weird when your medium is software.
13 I was briefly alarmed when there was talk of banning me from the computer lab for the remainder of my time at secondary school, which scared me because I was by now half-way through my boring childhood “life plan” to become a computer programmer by what seemed to be the appropriate route, and I feared that not being able to do a GCSE in a CS-adjacent subject could jeopardise that (it wouldn’t have).
14 That is, at least, my friends who were brave enough to carry on doing so after the teacher publicly (but inaccurately) described my alleged offences, seemingly as a warning to others.
15 Oh, the stories I probably shouldn’t tell! But here’s a teaser: when I built my first “beige box” (analogue phone tap hardware) I experimented with tapping into the phone line at my dad’s house from the outside. I carefully shaved off some of the outer insulation of the phone line that snaked down the wall from the telegraph pole and into the house through the wall to expose the wires inside, identified each, and then croc-clipped my box onto it and was delighted to discovered that I could make and receive calls “for” the house. And then, just out of curiosity to see what kinds of protections were in place to prevent short-circuiting, I experimented with introducing one to the ringer line… and took out all the phones on the street. Presumably I threw a circuit breaker in the roadside utility cabinet. Anyway, I patched-up my damage and – fearing that my dad would be furious on his return at the non-functioning telecomms – walked to the nearest functioning payphone to call the operator and claim that the phone had stopped working and I had no idea why. It was fixed within three hours. Phew!
I like it when the Internet says “yes, and”.
I like it when the Internet says “yes, but”.
I even like it when the Internet says “no, because”.
I’m not so keen when the Internet says “well, actually”,
(Probably because it reminds me of what
a shit I was in some not-yet-forgotten time.)
But I don’t like when the Internet rallies a brigade
To pick apart a character flaw I have, but hate,
Or to attack something I’m not, and expect me to defend.
So perhaps next time, start with “yes, and”, “yes, but”,
Or even “no, because”… or just say nothing, and
Remember what it means to connect with a human.
Highlight of my workday was debugging an issue that turned out to be nothing like what the reporter had diagnosed.
The report suggested that our system was having problems parsing URLs with colons in the pathname, suggesting perhaps an encoding issue. It wasn’t until I took a deep dive into the logs that I realised that this was a secondary characteristic of many URLs found in customers’ SharePoint installations. And many of those URLs get redirected. And SharePoint often uses relative URLs when it sends redirections. And it turned out that our systems’ redirect handler… wasn’t correctly handling relative URLs.
It all turned into a hundred line automated test to mock SharePoint and demonstrate the problem… followed by a tiny two-line fix to the actual code. And probably the most-satisfying part of my workday!
This morning it took me three attempts to put on a t-shirt the right way around.
I don’t think I slept too well.
I have a credit card with HSBC1. It doesn’t see much use2, but I still get a monthly statement from them, and an email to say it’s available.
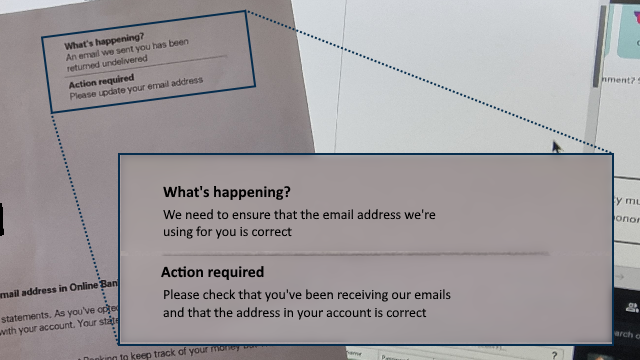
Not long ago I received a letter from them telling me that emails to me were being “returned undelivered” and they needed me to update the email address on my account.
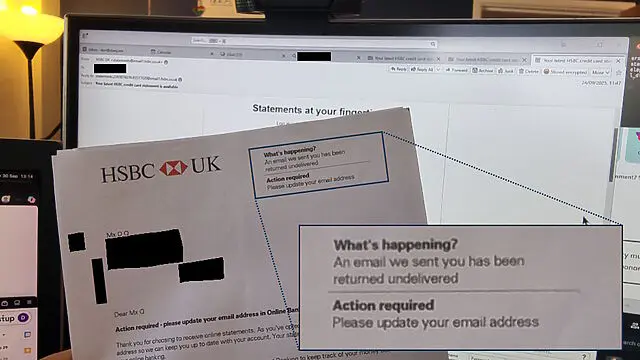
I logged into my account, per the instructions in the letter, and discovered my correct email address already right there, much to my… lack of surprise3.
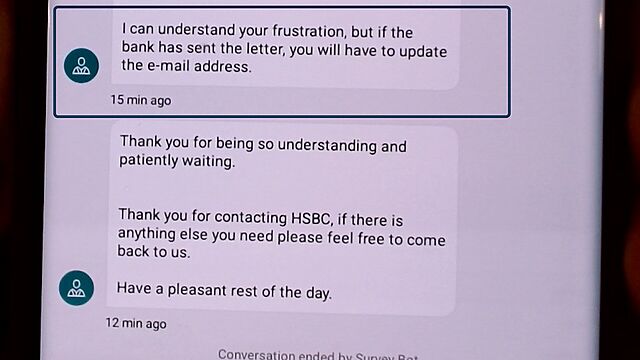
So I kicked off a live chat via their app, with an agent called Ankitha. Over the course of a drawn-out hour-long conversation, they repeatedly told to tell me how to update my email address (which was never my question). Eventually, when they understood that my email address was already correct, then they concluded the call, saying (emphasis mine):
I can understand your frustration, but if the bank has sent the letter, you will have to update the e-mail address.
This is the point at which a normal person would probably just change the email address in their online banking to a “spare” email address.
But aside from the fact that I’d rather not4, by this point I’d caught the scent of a deeper underlying issue. After all, didn’t I have a conversation a little like this one but with a different bank, about four years ago?
So I called Customer Services directly5, who told me that if my email address is already correct then I can ignore their letter.
I suggested that perhaps their letter template might need updating so it doesn’t say “action required” if action is not required. Or that perhaps what they mean to say is “action required: check your email address is correct”.
So anyway, apparently everything’s fine… although I reserved final judgement until I’d seen that they were still sending me emails!
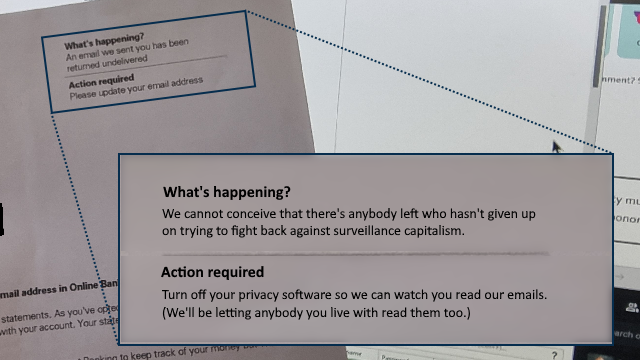
I think I can place a solid guess about what went wrong here. But it makes me feel like we’re living in the Darkest Timeline.

I dissected HSBC’s latest email to me: it was of the “your latest statement is available” variety. Deep within the email, down at the bottom, is this code:
<img src="http://www.email1.hsbc.co.uk:8080/Tm90IHRoZSByZWFsIEhTQkMgcGF5bG9hZA==" width="1" height="1" alt=""> <img src="http://www.email1.hsbc.co.uk:8080/QWxzbyBub3QgcmVhbCBIU0JDIHBheWxvYWQ=" width="1" height="1" alt="">
What you’re seeing are two tracking pixels: tiny 1×1 pixel images, usually transparent or white-on-white to make them even-more invisible, used to surreptitiously track when somebody reads an email. When you open an email from HSBC – potentially every time you open an email from them – your email client connects to those web addresses to get the necessary images. The code at the end of each identifies the email they were contained within, which in turn can be linked back to the recipient.
You know how invasive a read-receipt feels? Tracking pixels are like those… but turned up to eleven. While a read-receipt only says “the recipient read this email” (usually only after the recipient gives consent for it to do so), a tracking pixel can often track when and how often you refer to an email6.
If I re-read a year-old email from HSBC, they’re saying that they want to know about it.
But it gets worse. Because HSBC are using http://, rather than https:// URLs for their tracking pixels, they’re also saying that every time you read an email
from them, they’d like everybody on the same network as you to be able to know that you did so, too. If you’re at my house, on my WiFi, and you open an email from HSBC, not
only might HSBC know about it, but I might know about it too.
An easily-avoidable security failure there, HSBC… which isn’t the kind of thing one hopes to hear about a bank!
But… tracking pixels don’t actually work. At least, they doesn’t work on me. Like many privacy-conscious individuals, my devices are configured to block tracking pixels (and a variety of other instruments of surveillance capitalism) right out of the gate.
This means that even though I do read most of the non-spam email that lands in my Inbox, the sender doesn’t get to know that I did so unless I choose to tell them. This is the way that email was designed to work, and is the only way that a sender can be confident that it will work.
But we’re in the Darkest Timeline. Tracking pixels have become so endemic that HSBC have clearly come to the opinion that if they can’t track when I open their emails, I must not be receiving their emails. So they wrote me a letter to tell me that my emails have been “returned undelivered” (which seems to be an outright lie).
Surveillance capitalism has become so ubiquitous that it’s become transparent. Transparent like the invisible spies at the bottom of your bank’s emails.
So in summary, with only a little speculation:
Instead of sending me a misleading letter about undelivered emails, perhaps a better approach for HSBC could be:
Also, to quote your own principles once more: when you make a mistake like assuming your spying is a flawless way to detect the validity of email addresses, perhaps you should “be transparent with our customers and other stakeholders about how we use their data”.
Wouldn’t that be better than writing to a customer to say that their emails are being returned undelivered (when they’re not)… and then having your staff tell them that having received such an email they have no choice but to change the email address they use (which is then disputed by your other staff)?
</rant>
1 You know, the bank with virtue-signalling multiculturalism that we used to joke about.
2 Long, long ago I also had a current account with HSBC which I forgot to close when I switched banks… 20 years ago… and I possibly still owe them for the six pence the account was in debt at the time.
3 After all, I’d been reading their emails!
4 After all, as I’ll stress again: the email address HSBC have for me, and are using, is already correct.
5 In future, I’ll just do this in the first instance. The benefits of live chat being able to be done “in the background” while one gets on with some work are totally outweighed when the entire exchange takes an hour only to reach an unsatisfactory conclusion, whereas a telephone call got things sorted (well hopefully…) within 10 minutes.
6 A tracking pixel can also collect additional personal information about you, such as your IP address at the time that you opened the email, which might disclose your location.
7 It could be even worse still, actually! A sophisticated attacker could “inject” images into the bottom of a HSBC email; those images could, for example, be pictures of text saying things like “You need to urgently call HSBC on [attacker’s phone number].” This would allow a scammer to hijack a legitimate HSBC email by injecting their own content into the bottom of it. Seriously, HSBC, you ought to fix this.
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.

Have you ever wished there were more to the internet than the same handful of apps and sites you toggle between every day? Then you’re in for a treat.
Welcome to the indie web, a vibrant and underrated part of the internet, aesthetically evocative of the late 1990s and early 2000s. Here, the focus is on personal websites, authentic self-expression, and slow, intentional exploration driven by curiosity and interest.
These kinds of sites took a backseat to the mainstream web around the advent of big social media platforms, but recently the indie web has been experiencing a revival, as more netizens look for connection outside the walled gardens created by tech giants. And with renewed interest comes a new generation of website owner-operators, intent on reclaiming their online experience from mainstream social media imperatives of growth and profit.
…
I want to like this article. It draws attention to the indieweb, smolweb, independent modern personal web, or whatever you want to call it. It does so in a way that inspires interest. And by way of example, it features several of my favourite retronauts. Awesome.
But it feels painfully ironic to read this article… on Substack!
Substack goes… let’s say half-way… to representing the opposite of what the indieweb movement is about! Sure, Substack isn’t Facebook or Twitter… but it’s still very much in the same place as, say, Medium, in that it’s a place where you go if you want other people to be in total control of your Web presence.
The very things that the author praises of the indieweb – its individuality and personality, its freedom control by opaque corporate policies, its separation from the “same handful of apps and sites you toggle between every day” – are exactly the kinds of things that Substack fails to provide.
It’s hardly the biggest thing to hate about Substack, mind – that’d probably be their continued platforming of Covid conspriacy theorists and white nationalist hate groups. But it’s still a pretty big irony to hear the indieweb praised there!
Soo… nice article, shame about the platform it’s published on, I guess?