My upcoming RockMonkey WikiGame is set to impress, I hope: I’m aiming for the most adventurous WikiGame ever created. There’s a screenshot available of the kind of thing I’ve got working so far. Probably a few weeks from completion, though.
Tag: technology
Big.McLargeHuge Lives
Nobody on Earth, not even Gareth, knows or understands what happened to cause the server problems on Big.McLargeHuge yesterday, but, as usual, everybody’s blaming me. My apologies to everybody who was inconvenienced by the problems. It’s amazing how much damage can be caused by a MySQL server going down… almost all the sites on McLargeHuge are database-powered, not to mention the DNS server (the death of which caused problems accessing a certain other server I run [I’ve put in a few backup systems to help with this kind of thing in future]) and the mail server (which caused a ripple effect of delaying e-mails across the network)…
In any case; despite having no idea what caused the fault in the first place, steps are being taken to ensure that so much damage can not be caused again. Those who need to know know who to ask. Thanks to Gareth for all his help.
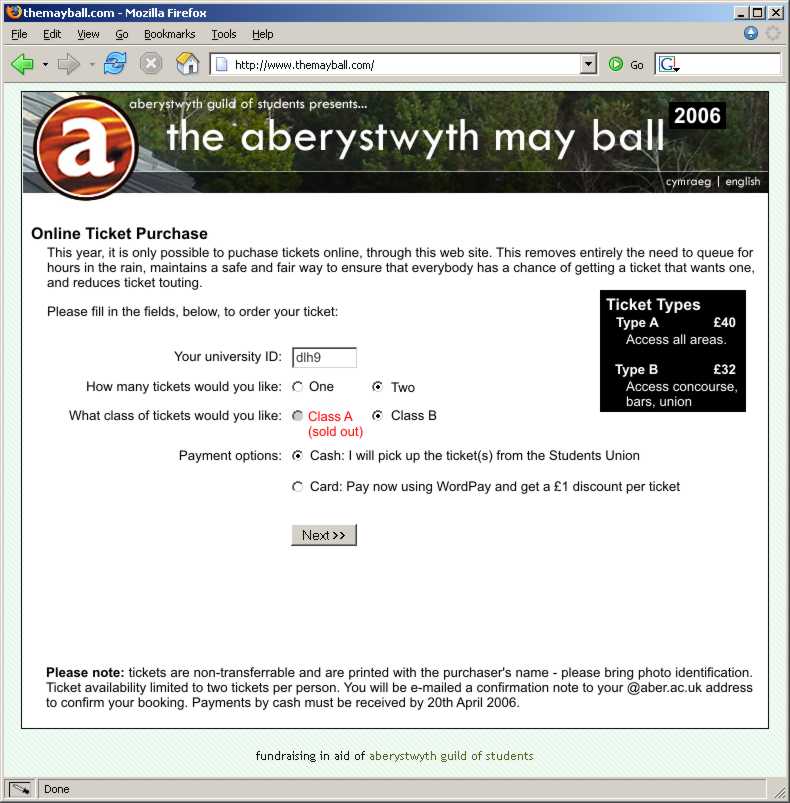
How To Sell May Ball Tickets
Every year the Students Union here in Aberystwyth puts on the May Ball, an excuse to dress up and party if ever I saw one, for students. For the last few years this has been held on-campus, in the Arts Centre, Students Union, and the concourse in-between the two. Live music and shows, dancing, and a fairground… and hundreds of students in ball gowns and tuxedos… Since the event had been moved “on campus” there have been less tickets available than ever, and demand grows steadily higher. As a result, students queue for hours to get their tickets.
This year, tickets began to be served at 10am, but the queue was 270 people long by forming by midnight: yes, people were willing to stand, all night, for ten hours, to be first in a queue for May Ball tickets. The Students Union have, of course, monopolised on the situation and will be selling drinks to the people queuing. Hey; let’s charge them twice.
Another recent problem has been that of ticket touting. Tickets sell for under £40, but can be re-sold to those desperate to go for as much as £100. Last year, the Students Union would not allow more than 8 tickets to be bought in a single transaction (and with queues so long, there’s no chance of queuing again), but that still meant that sly touts could easily earn up to £480 for a few hours work. This year, only four tickets can be bought by any single person, but this simply resulted in a longer queue, sooner, and I don’t think it’ll stop touting (if I was going to the May Ball, and therefore needed to queue anyway, I would buy my full allotted four tickets, regardless of how many people I was actually purchasing tickets for… and I know of dozens of others who follow this methodology every year, meaning that even as demand goes up, the touts take an even larger share of the profits).
Thankfully, I’ve been to the May Ball once and I’ll happily get by without ever going again. But I got to thinking, having seen the lunacy in those students who’ve spent all of this morning and all of last night queueing, that this isn’t the best way to be arranging this event…
A Better Way
Here’s how it should be done. All the tickets should be sold online, by the Students Union. If you want to buy tickets, you connect to their web site and fill in the following details:
- Your university user name – this ensures that your ticket is ‘reserved’ for you, and that you cannot buy multiple tickets.
- The number and type of tickets you want to buy – only two tickets maximum per person.
- How you’d like to pay and obtain the tickets: you can pay online (and have them posted to you) or you can collect them from the union building for up to a week afterwards and pay in cash.
An e-mail is sent to your university e-mail address to confirm that it really was you who ordered the tickets (and not somebody ordering in your name). If this is not replied to within 24 hours (as will be explained in the e-mail), the order is cancelled. The tickets (which are posted to you or collected from the union) are printed with “Your Name”, and “Guest of Your Name”, eliminating the risk of touting (assuming that reasonable checks are made by security at the gate – just checking the identity of every fifth person in would act as sufficient deterrent to those who would like to go to the ball using a ticket in somebody else’s name).
The e-mail confirmation also gives people a chance to change their mind: if their friends, who they wanted to go with, were unable to get tickets before they all sold out, for example, they would know about it and be able to cancel their order. But it would also ensure the identity of the purchaser without requiring them to pass their password over the network. Students collecting tickets from the union would have to produce photo ID.
Those tickets remaining unsold after the web server is hammered by requests for tickets (for example, those cancelled or released later) would all be sold in a “second wave” (which would be announced in advance).
It is terribly unfair for the union to make students stand out in the cold and the rain, without sleep, to get tickets to an event; it could even be argued as discriminatory (whereas the University ensures that all students have the capacity and tools to use an internet connection). There would be no queues, no touts, and no unfairness. There would be no fights for the limited amount of cash in the on-campus cashpoints. The union would save money in ticket salespeople and policing the queue. And a system like this could be implemented for them for a sum of money that could be measured in the hundreds, not the thousands, of pounds. Hell; I will quote them for it, if they ask: I’ve already knocked up a prototype. Why not send a message to the May Ball organisers and tell them what a good idea it would be, particularly if it would make the difference to you, personally, about going to the May Ball.
They still won’t listen.
GMail Accounts
People have asked me for GMail invites again, but one of these people’s @aber.ac.uk e-mail address doesn’t seem to be working, says GMail, so here are some “ready to pick up”:
- Invite 1 (used)
- Invite 2 (used)
- Invite 3 (used)
- Invite 4 (used)
- Invite 5
- Invite 6
- Invite 7
- Invite 8
- Invite 9
- Invite 10
Get ’em while they’re hot. If one doesn’t work, try another. If they all don’t work, leave a comment (and pull your finger out next time).
Hollywood Pizza And BT Online Billing
If only BT.com online billing provided an XML feed… we could integrate our Hollywood Pizza order call times and lengths into the Troma Night web site.
Probably not a good thing, actually.
DVI-VGA Adapter
 Troma Night tonight could really do with a
DVI-VGA adapter, like the one pictured to the right. I have two of them, somewhere. If you were part of the tidy-up squad and you remember seeing it, or if you have one that
you can lend to me for the evening, it would be much appreciated.
Troma Night tonight could really do with a
DVI-VGA adapter, like the one pictured to the right. I have two of them, somewhere. If you were part of the tidy-up squad and you remember seeing it, or if you have one that
you can lend to me for the evening, it would be much appreciated.
Google Wants Your DIY Porn Videos
Got home videos? Send them to Google! That’s the message that Google co-founder Larry Page is trying to put out.
In anticipation of launching a “video search” system, Google wants a stack of material on which they can test their “video spider” – a program which will hunt for keywords (spoken, or on-screen) in video material, so that it’s searchable in much the same way as web pages already are.
Fucking weird.
Ceefax On Scatmania
Do you remember Ceefax, that wonderful service from the BBC that seemed so cool until you discovered the internet? Well I do. And so does a Dutch consultant who set up a system, on the web, for searching Ceefax pages.
Well; in any case; I thought that his site was fun (in a nostalgic kind-of way) but hard-to-navigate, so I’ve developed a sensible front-end that’s far more reminiscent of the way Ceefax works: Ceefax Browser On Scatmania. Give it a go.
Norfolk
Claire and I’s grand tour of the United Kingdom brought us yesterday to Terrington St. Clement, near Kings’ Lynn, in Norfolk, where Claire’s dad lives.
As I anticipated, this has resulted in me here, too, helping to repair computers. Claire’s dad’s PC was a mess – Ad-Aware reported 183 malware/adware programs, Norton Anti-Virus reported 10 threats (2 of which were actually installed viruses). I don’t know what the solution is to the problems caused by hundreds of thousands of new people – who do not know about the risks – appearing on the internet, but I hope that somebody works it out soon: even the BBC have started to take notice of the increasing problem of “zombie” networks, particularly in the UK, which lead to denial of service attacks, spam floods, breaches of privacy, and annoying pop-up ads.
And there’s no excuse, really – Windows users can get AVG (anti-virus), ZoneAlarm (firewall), Ad-Aware (anti-malware/adware), Firefox (web browser) and Thunderbird (e-mail client) and be safer by hundreds of orders of magnitude than they are with Internet Explorer and a wide-open pipe. And all of this software is free. With the increase of the awareness of this problem by mainstream news sources, you’d think it would spur people into protecting themselves (just like the coverage of the “War On Terror” by mainstream media made people paranoid about radiological/chemical/biological terrorist attacks). Ah well.
In any case: we’ve been traipsing around North Norfolk, meeting people and eating excessively. I’ve just about recovered from a minor leg sprain I sustained while ice skating in Preston earlier this week, and all is well.
Glad to hear that Sian‘s Troma Night went well (can’t remember where I heard that from). Missing all you Aberites. Hope to see you all soon.
Preston
Things achieved so far:
- Got to Preston in three hours, which is pretty good going. We got stuck behind some idiots who seemed to think that “national speed limit” meant 30mph for awhile, but by the time we got to the big roads it was plain sailing. Without sails. Or a boat.
- Fixed my dad’s wireless network. He has a wireless network comprising his desktop PC, each of my sisters’ desktop PCs, and an ADSL router. Having recently gotten a new laptop he wanted to connect this to the
network, too, so he got an old USB wireless adapter he had and plugged it in. Hmm.. can’t seem to join the network: can see it, but can’t
join it. So he goes and buys a new adapter – this time, one which was of the same brand as the ones of which his network was already composed. Nope, still nothing. Eventually, has
patience at an end, he borrowed my sister’s adapter… and it worked fine.If you’re a network geek, see if you can think what the problem might be before you read on.
The problem was that his network had been set up to use MAC address locking – preventing access to the router by anything but a list of particular hardware devices (or, for non-geeks: every piece of networking equipment has a supposedly globally unique number assigned to it when it is manufactured: my dad’s router had been configured only to allow particular numbers to connect to it ). So, it was a simple challenge to allow these new devices access to his network. The net result seemed to be that there was one useless wireless adapter.
But here’s where things got really silly: it later turned out that his new laptop had a built-in wireless adapter, and he’d never known. All he had to do was actually install the drivers for it (to be fair, you’d think on a pre-built laptop they might have done that for him) and voila: he was on the network… two useless wireless adapters.
- Installed Firefox as the default browser on all of the IE-default machines we’ve come across.
- Met the puppies (4), the chickens (3½), the rabbit (1, with 3 others loose somewhere in the scrubland behind the house – kids on the neighbourhood sometimes catch one – at great risk and loss of blood [theirs’, not the rabbit’s] – and ransom it back), and the hermit crabs (2) for the first time. Re-met the dog (1), and the cats (4… 5…? 6??? who knows). My mum’s house is becoming quite the menagerie. I’ll try to get some pictures online before we leave here on Monday.
- Taught my parents to play Fluxx. My dad turns out to be surprisingly… lucky… at it.
- Drank mead from the holy isle of Lindisfarne, where my dad has recently been.
By the way – Paul: I’ve left a key to TheFlat with Bryn, so there’s no need to camp out at the cafe all day in anticipation of Troma Night tonight: have a good one, guys!
Right – off to watch Spongebob Squarepants.
Physical Device Fingerprinting Over TCP
A PhD student in San Deigo has written a fascinating paper which will spook internet anonymity freaks – Remote Physical Device Fingerprinting – which describes how a physical computer can be uniquely identified on the internet, regardless of operating system, IP address, or data sent, just by looking carefully at it’s TCP packets (which contain the data for a large amount – perhaps a majority – of the internet’s traffic, including all web and e-mail traffic).
The technique works by observing the deviation in the timestamps sent (in accordance with the widely-adopted RFC 1323: TCP Extensions for High Performance, specified back in 1992). Each computer’s hardware clock is made from a separate piece of quartz, and each quartz crystal is unique in it’s imperfections. By measuring these imperfections across the internet, it’s possible (with enough sample data) to identify a computer individually, which has implications both good (computer forensics) and bad (anonymity).
The paper itself [PDF] is well worth reading. And, for those that are paranoid about their anonymity online, here’s how to “turn off” this feature of TCP for Windows 2000, Windows XP, and Linux:
- Windows 2000/XP – Run RegEdit; navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters; add (or edit, if already present) the DWORD “Tcp1323Opts” to 1. This disables TCP timestamps, but leaves Window Scaling (a really useful TCP/IP enhancement) enabled.
-
Linux –
echo 0 > /proc/sys/net/ipv4/tcp_timestamps
Of course, the absence of timestamps from your machine may, if you’re in a small enough sample group, single you out even more, but at least you’re not globally unique any more; which from an anonymity perspective is a really good thing.
Things Bots Shouldn’t Learn
This afternoon, I’ve taught Iggy, the robot who looks after the RockMonkey ChatRoom:
- How to play The Game. Damn – I’m out. He’s not very good at it, and, by proxy, neither am I.
- Comprehension of facts expressed as “concept ARE fact”, rather than “concept IS fact”, and about knowing “who” people are (ask “Iggy, who is Ava_Work”, for example, or teach him who other people are…).
The by-product of this is that I’ve been learning to program in Tcl. And as a result, discovering why nobody writes in Tcl. Here’s a quote from bash.org, which I found in the bMotion source code:
<Procyan> is there like 1 person on earth that knows tcl/tk and is writing all of the apps?
<unSlider> procyan: no, there are a bunch of people who dont know tcl/tk but are writing apps for it anyway
Opera 8’s Solution To IDN Exploit
I’m sure you’ve all seen the recent Internationalized Domain Name exploit, which affects most web browsers (except for Internet Explorer – shocker! – because it doesn’t yet have the power to support internationalized domain names): if you haven’t, why not visit paypal.com – looks just like the real thing; doesn’t it: the browser bar says you’re at PayPal’s real site, but you’re not. That first ‘a’ in the name is an international character (actually the letter ‘a’ from the Cyrillic character set, which is just slightly different from a Western ‘a’, if you look closely. Of course, this leads to potentially thousands of dangerous phishing exploits, tricking users into exposing their bank account details to random Nigerians.
Opera, makers of a stunning web browser that I’m not quite sure I should be abandoning yet, have announced their solution to this problem (which isn’t actually a web browser problem at all, but a specification problem): IDN domain names from outside of places which are expected to need then (e.g. dot-jp, etc.) will be displayed longhand, and secure sites (https) will display their certificate holder’s name – longhand – alongside the domain name in the address bar.
Of course, unless you’re using Opera 8 beta, the only way to be sure you’re safe from this exploit is to manually type in every link you follow.
This Has GOT To Be Anti-Trust/FUD
This screenshot taken from Microsoft Anti-Spyware:
[screenshot removed – later turned out to be a fake]
MEng Dissertation – Hamster Music
No, I’m not talking about that god-awful de-da-de-da-de-do-do-do de-da-de-do do thingy: I’m talking about this ingenious MEng dissertation project, in which the student hooked up six hamsters to a MIDI device and, with some clever hardware and software, used their movements to compose music. If you look at the site, be sure to download the video clip or at least a sample of the music produced!