The comprehensive @id3 v2 system for #MP3 metadata doesn’t seem to have an “explicit content” flag. I’m using an experimental XRAT frame (with a ‘1’ or ‘0’) for now, but I
wonder if anyone’s already “solved” this in a better way?
Blog
EGXchange – a digital EGX wallet
I’ve just launched EGXchange.org, a digital wallet for new currency Emma Goldcoin, which I’ve mentioned previously (including a discussion with the author in my comments section).
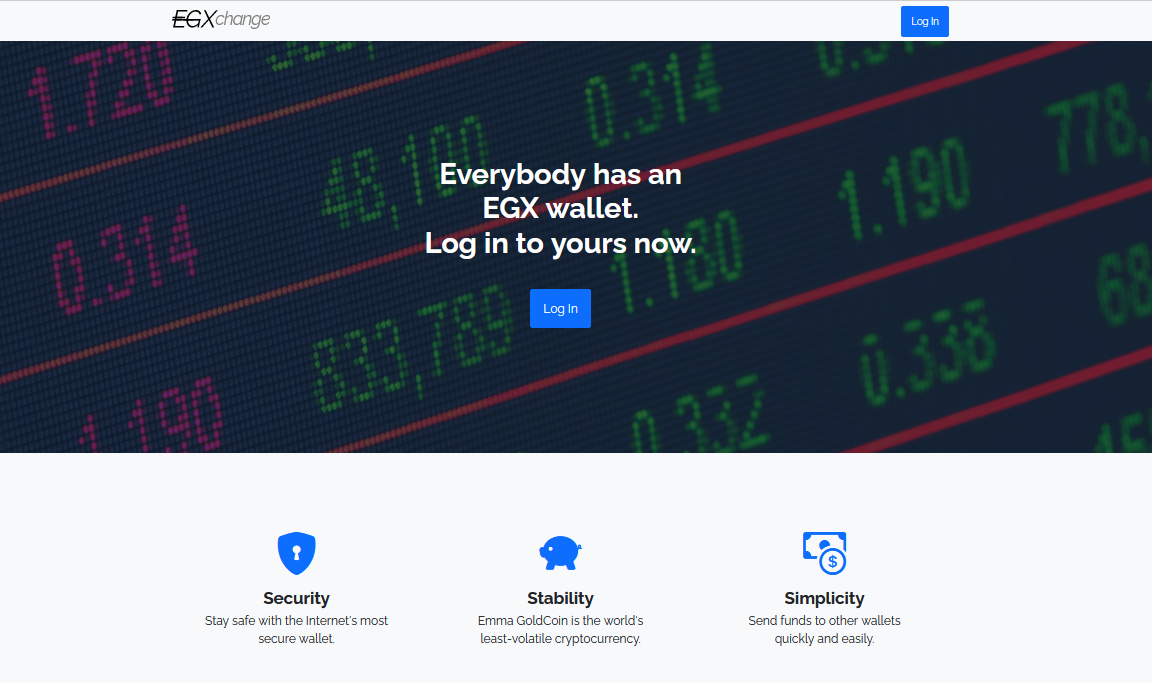
You can install it as an offline-first progressive web application, which means that this could be the first ever digital currency to have an app that works without an Internet connection. That’s probably something no other digital currency can claim to have, right?
Here’s what it looks like if I send 0.1 EGX to my friend Chris using the app:
Naturally, I wouldn’t be backing Emma Goldcoin if it didn’t represent such a brilliant step up better-known digital currencies like Bitcoin, Ripple, and Etherium. Specific features unique to Emma Goldcoin include:
- Using it doesn’t massively contribute to energy wastage and environmental damage.
- It doesn’t increase the digital divide by helping early adopters at the expense of late adopters.
- It’s entirely secure: it’s mathematically impossible to “steal”EGX.
- Emma Goldcoin is so simple that you don’t even need a computer to use it: it “just works”.
Sure, it’s got its downsides, and I’d encourage you to read the specification if you’d like to learn more about what those are. Or if you already know what EGX is all about and just want to try a new way to manage your portfolio, give my new site EGXchange.org a go!
Emma GoldCoin
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
…
EGX fixes all the problems with all the existing cryptocurrencies once and for all. In particular it fixes the problems around security, environmental impact and ease of use that beset all other known blockchain-based cryptocurrency offerings.
- Security
Due to the unique way in which the EGX blockchain is constructed, EGX cannot be hacked and will never be hacked. Period. There are and never will be any security issues with EGX. No other cryptocurrency on or off the planet can claim this.
- Environment
Whether based on Proof Of Work or Proof of Stake, all other blockchains have a non-negligible and non-zero environmental impact. EGX however is based on neither of these. Instead it is based on Proof Of Existence, described below. PoE has a minimum environmental impact that is provably zero. Individual EGX implementations may have greater environmental impact than this, but that is entirely on the implementor. EGX PoE can be as low as zero if you wish, and we can prove this.
- Ease Of Implementation
Due to its unique properties, no other cryptocurrency is or ever will be easier to implement and work with as EGX. This is not an empty claim – again, we can prove this.
…
Now here’s a cryptocurrency I can get behind. Shut up and take my money!
Dan Q found GC1WXE1 A Road Anarchy A417 – Stand & Deliver
This checkin to GC1WXE1 A Road Anarchy A417 - Stand & Deliver reflects a geocaching.com log entry. See more of Dan's cache logs.
Not the first place I looked! Came out this way, this morning, to find the nearby 2021-12-22 51 -2 geohashpoint (it’s about two kilometres West of this GZ) and, during my return journey, noticed that this cache was close by. TFTC.
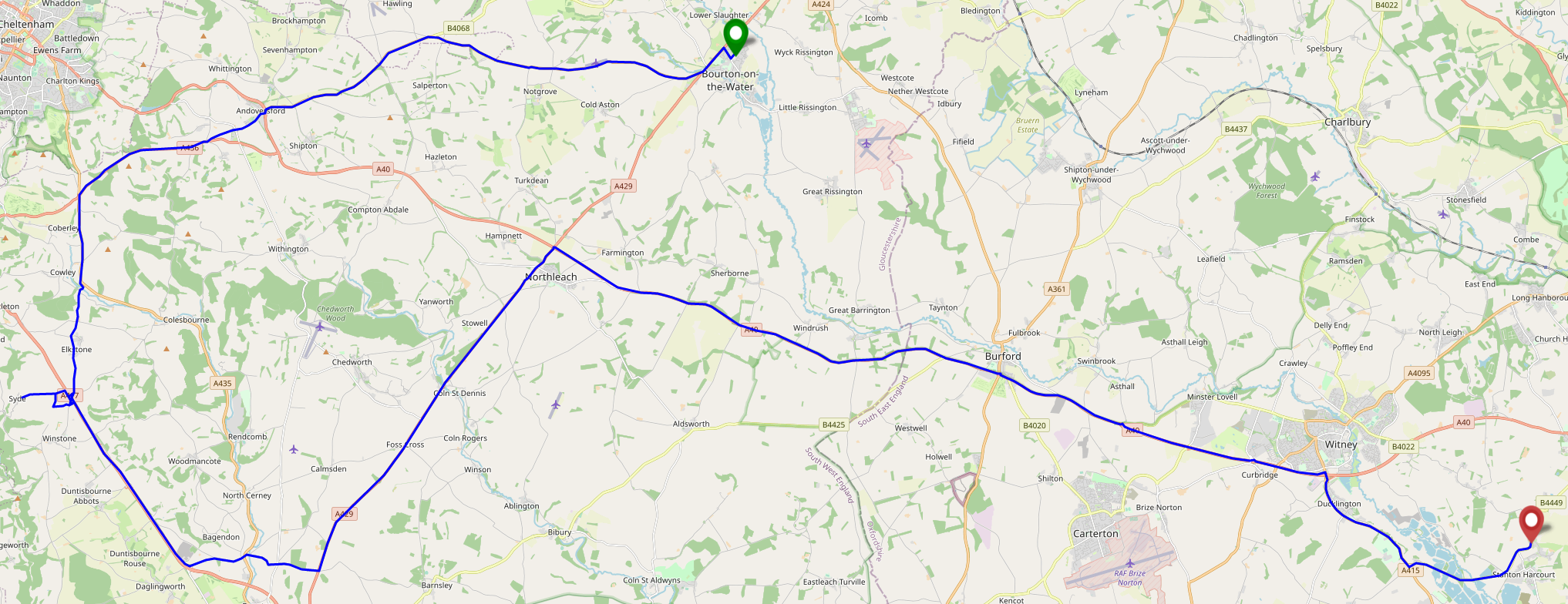
Geohashing expedition 2021-12-22 51 -2
This checkin to geohash 2021-12-22 51 -2 reflects a geohashing expedition. See more of Dan's hash logs.
Location
East side of Syde; side of a Syde Farm field.
Participants
Plans
I’m going to be going half way here anyway on an errand. Might as well enjoy a morning hike and expand my Minesweeper grid, if I can.
Expedition
Given that I was driving half way from home to this hashpoint to run an errand anyway, I figured I might as well push the battery on the EV a little further. Coming over the graticule line would, if successful, expand my Minesweeper score, and as it’s such a beautiful frosty morning it seemed like great conditions for a bit of an explore.
I’d hoped to drive most of the way to the hashpoint and only walk a short distance, but I soon discovered that the nearest road is signposted as being for access to Syde Farm only (and is narrow enough that passing a vehicle coming the other way would be extremely awkward), so I parked up near geocache GC1WXE1 and hiked along a frozen bridleway to get closer to the hashpoint.
Reached the hashpoint around 10:15, turned around, and headed back, nabbing the geocache on the way. By the time I reached the car my hands were freezing and it was only as I returned my GPSr to my coat pocket that I remembered that I’d been carrying my gloves all along.
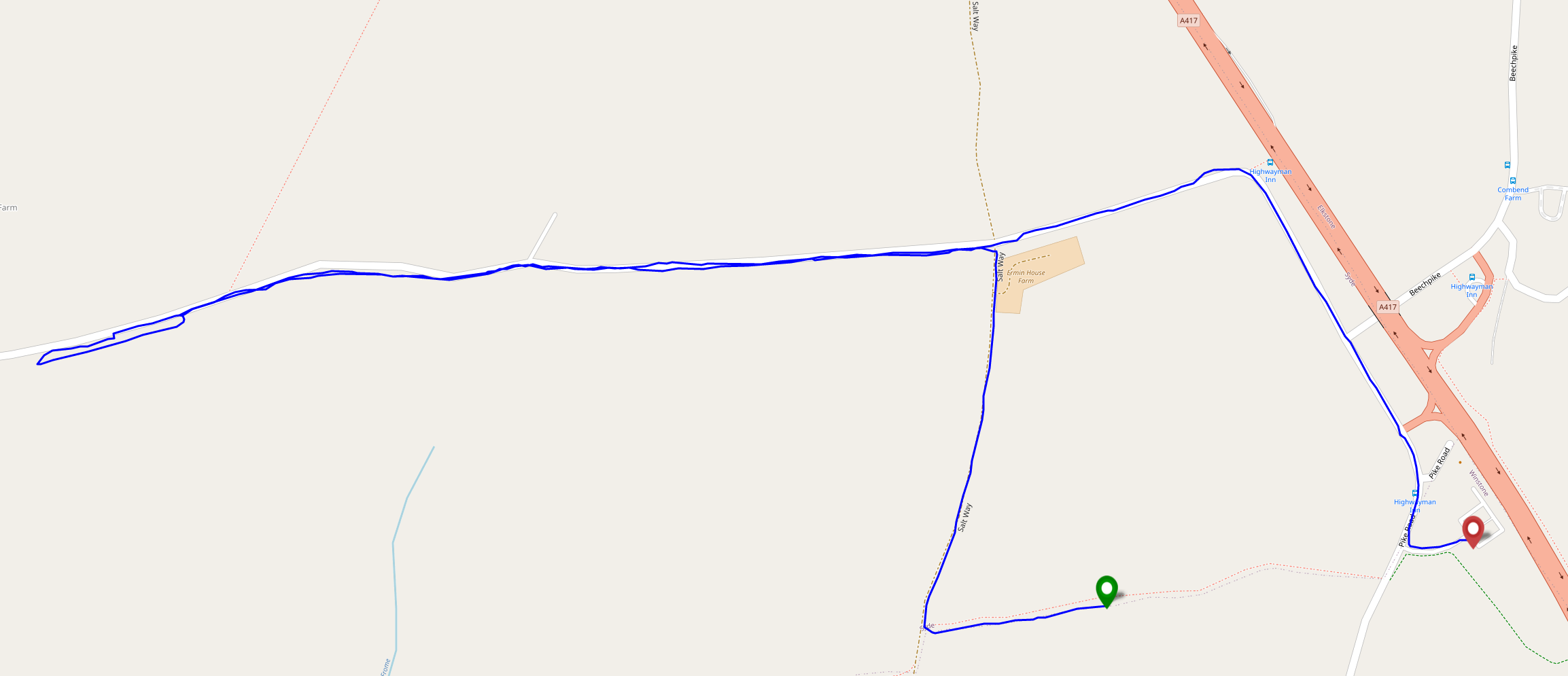
Tracklog
Entire journey
Walking part (after I remembered to start tracking it)
Photos
Taking a Jackbox Zoom Party to the Next Level
A love a good Jackbox Game. There’s nothing quite like sitting around the living room playing Drawful, Champ’d Up, Job Job, Trivia Murder Party, or Patently Stupid. But nowadays getting together in the same place isn’t as easy as it used to be, and as often as not I find my Jackbox gaming with friends or coworkers takes place over Zoom, Around, Google Meet or Discord.
There’s lots of guides to doing this – even an official one! – but they all miss a few pro tips that I think can turn a good party into a great party. Get all of this set up before your guests are due to arrive to make yourself look like a super-prepared digital party master.
1. Use two computers!

Using one computer for your video call and a second one to host the game (in addition to the device you’re using to play the games, which could be your phone) is really helpful for several reasons:
- You can keep your video chat full-screen without the game window getting in the way, letting you spend more time focussed on your friends.
- Your view of the main screen can be through the same screen-share that everybody else sees, helping you diagnose problems. It also means you experience similar video lag to everybody else, keeping things fair!
- You can shunt the second computer into a breakout room, giving your guests the freedom to hop in and out of a “social” space and a “gaming” space at will. (You can even set up further computers and have multiple different “game rooms” running at the same time!)
2. Check the volume
Connect some headphones to the computer that’s running the game (or set up a virtual audio output device if you’re feeling more technical). This means you can still have the game play sounds and transmit them over Zoom, but you’ll only hear the sounds that come through the screen share, not the sounds that come through the second computer too.
That’s helpful, because (a) it means you don’t get feedback or have to put up with an echo at your end, and (b) it means you’ll be hearing the game exactly the same as your guests hear it, allowing you to easily tweak the volume to a level that allows for conversation over it.
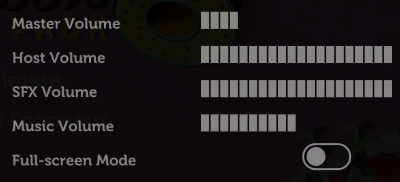
3. Optimise the game settings
Jackbox games were designed first and foremost for sofa gaming, and playing with friends over the Internet benefits from a couple of changes to the default settings.
Sometimes the settings can be found in the main menu of a party pack, and sometimes they’re buried in the game itself, so do your research and know your way around before your party starts.
Turn the volume down, especially the volume of the music, so you can have a conversation over the game. I’d also recommend disabling Full-screen Mode: this reduces the resolution of the game, meaning there’s less data for your video-conferencing software to stream, and makes it easier to set up screen sharing without switching back and forth between your applications (see below).
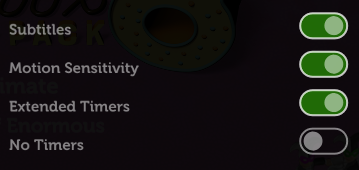
Turning on the Motion Sensitivity or Reduce Background Animations option if your game has it means there’ll be less movement in the background of the game. This can really help with the
video compression used in videoconferencing software, meaning players on lower-speed connections are less-likely to experience lag or “blockiness” in busy scenes.
It’s worth considering turning Subtitles on so that guests can work out what word they missed (which for the trivia games can be a big deal). Depending on your group, Extended Timers is worth considering too: the lag introduced by videoconferencing can frustrate players who submit answers at the last second only to discover that – after transmission delays – they missed the window! Extended Timers don’t solve that, but they do mean that such players are less-likely to end up waiting to the last second in the first place.
Finally: unless the vast majority or all of your guests are in the USA, you might like to flip the Filter US-Centric Content
switch so that you don’t get a bunch of people scratching their heads over a cultural reference that they just don’t get.
By the way, you can use your cursor keys and enter to operate Jackbox games menus, which is usually easier than fiddling with a mouse.
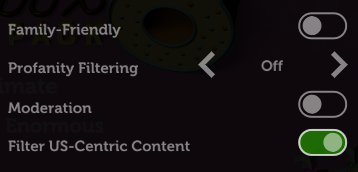
4. Optimise Zoom’s settings
Whatever videoconferencing platform you’re using, the settings for screen sharing are usually broadly similar. I suggest:
- Make sure you’ve ticked “Share sound” or a similar setting that broadcasts the game’s audio: in some games, this is crucial; in others, it’s nice-to-have. Use your other computer to test how it sounds and tweak the volume accordingly.
- Check “Optimize for video clip”; this hints to your videoconferencing software that all parts of the content could be moving at once so it can use the same kind of codec it would for sending video of your face. The alternative assumes that most of the screen will stay static (because it’s the desktop, the background of your slides, or whatever), which works better with a different kind of codec.
- Use “Portion of Screen” sharing rather than selecting the application. This ensures that you can select just the parts of the application that have content in, and not “black bars”, window chrome and the like, which looks more-professional as well as sending less data over the connection.
- If your platform allows it, consider making the mouse cursor invisible in the shared content: this means that you won’t end up with an annoying cursor sitting in the middle of the screen and getting in the way of text, and makes menu operation look slicker if you end up using the mouse instead of the keyboard for some reason.
Don’t forget to shut down any software that might “pop up” notifications: chat applications, your email client, etc.: the last thing you want is somebody to send you a naughty picture over WhatsApp and the desktop client to show it to everybody else in your party!
Dan Q found GC5VKVN Walk by the Firehouse #4
This checkin to GC5VKVN Walk by the Firehouse #4 reflects a geocaching.com log entry. See more of Dan's cache logs.
I first tried to find this cache back in 2018, but the cache container had been destroyed leaving only a fragment of it left. Today, as I was out on a lunchtime cycle nearby anyway, I decided to come and give it another go. I’d left my primary GPSr at home so I had to use my phone, which for some reason was declaring my position to be about 22m off target (and well into the fields, based on local aerial photography!) but my memory of the hiding place – coupled with a quick check of the clue – confirmed I was looking in the right place. I don’t know if it’s hidden higher up now or if I’ve just gotten shorter but it was a bit of a stretch to reach! SL, TFTC.
Dan Q couldn’t find GC9K2D0 The Footpath Wonder
This checkin to GC9K2D0 The Footpath Wonder reflects a geocaching.com log entry. See more of Dan's cache logs.
Saw the notification pop up and thought this was an obvious FTF opportunity, so me and a geokid zipped out and mounted a search. After about 20 minutes of hunting we double checked hint cache details – only a D2/T1: maybe we’re not on form today. Or maybe something else is amiss: a brand new cache by a cacher with no finds and no (other) hides, with no description and no hint? Did this perhaps get published prematurely? We’ll come back later in the week for another go, but for now this one’s a sad-face for us.
Dan Q found GC1E9YX Uninhabited Island
This checkin to GC1E9YX Uninhabited Island reflects a geocaching.com log entry. See more of Dan's cache logs.
Geosense sent me straight to this one during a short visit to Stratford. Some fellow volunteers and I stayed at the hotel last night for our AGM and Christmas party and I couldn’t resist coming out to find this before heading back to Oxfordshire. TFTC.
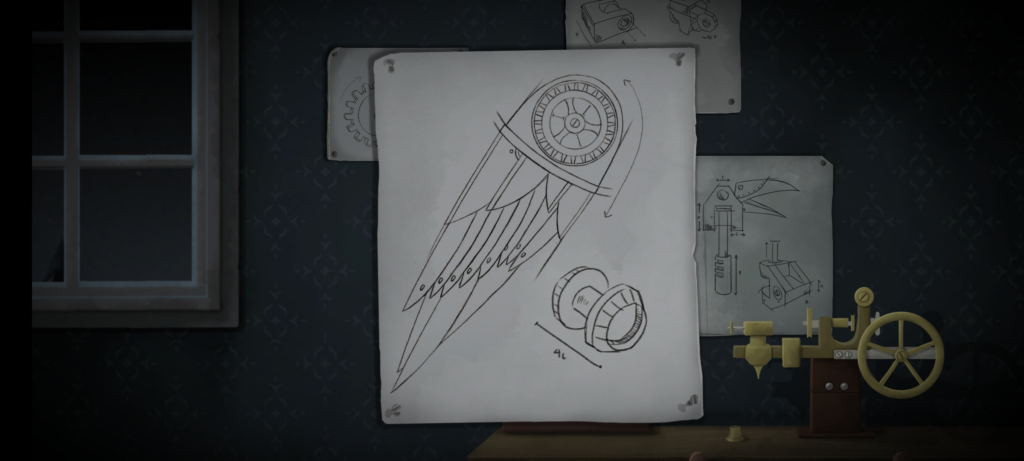
Tick Tock
Looking for something with an “escape room” vibe for our date night this week, Ruth and I tried Tick Tock: A Tale for Two, a multiplayer simultaneous cooperative play game for two people, produced by Other Tales Interactive. It was amazing and I’d highly recommend it.

The game’s available on a variety of platforms: Windows, Mac, Android, iOS, and Nintendo Switch. We opted for the Android version because, thanks to Google Play Family Library, this meant we only had to buy one copy (you need it installed on both devices you’re playing it on, although both devices don’t have to be of the same type: you could use an iPhone and a Nintendo Switch for example).
The really clever bit from a technical perspective is that the two devices don’t communicate with one another. You could put your devices in flight mode and this game would still work just fine! Instead, the gameplay functions by, at any given time, giving you either (a) a puzzle for which the other person’s device will provide the solution, or (b) a puzzle that you both share, but for which each device only gives you half of the clues you need. By working as a team and communicating effectively (think Keep Talking and Nobody Explodes but without the time pressure), you and your partner will solve the puzzles and progress the plot.
(We’re purists for this kind of puzzle game so we didn’t look at one another’s screens, but I can see how it’d be tempting to “cheat” in this way, especially given that even the guys in the trailer do so!)
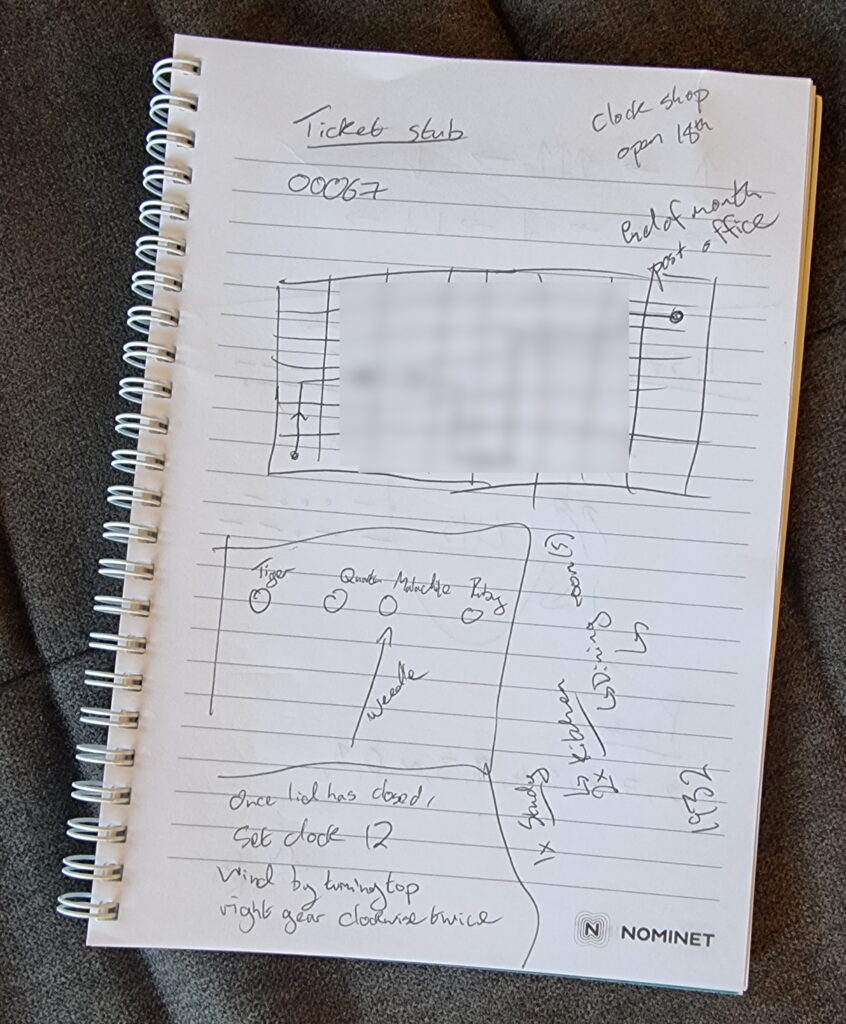
The puzzles start easy enough, to the extent that we were worried that the entire experience might not be challenging for us. But the second of the three acts proved us wrong and we had to step up our communication and coordination, and the final act had one puzzle that had us scratching our heads for some time! Quite an enjoyable difficulty curve, but still balanced to make sure that we got to a solution, together, in the end. That’s a hard thing to achieve in a game, and deserves praise.
The plot is a little abstract at times and it’s hard to work out exactly what role we, the protagonists, play until right at the end. That’s a bit of a shame, but not in itself a reason to reject this wonderful gem of a game. We spent 72 minutes playing it, although that includes a break in the middle to eat a delivery curry.
If you’re looking for something a bit different for a quiet night in with somebody special, it’s well worth a look.
“DOONT” — A Bad Lip Reading of Dune
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
You may remember that I was excited to hear about the upcoming release of Dune (which I suppose should be called Dune: Part One). It turns out to be excellent and I’d recommend it to anybody.
But once you’ve seen it and while you’re in the two-year wait for Dune: Part Two (argh!), can I suggest you also enjoy this wonderful creation by the folks at Bad Lip Reading, whose work I’ve plugged before. Note: minor spoilers (amazingly) if you haven’t seen Dune yet.
Note #19700
How did it take me years of working-from-home before I thought to install one of these in my desk? Brilliant.
Pronouns in Three Rings
The Old Way
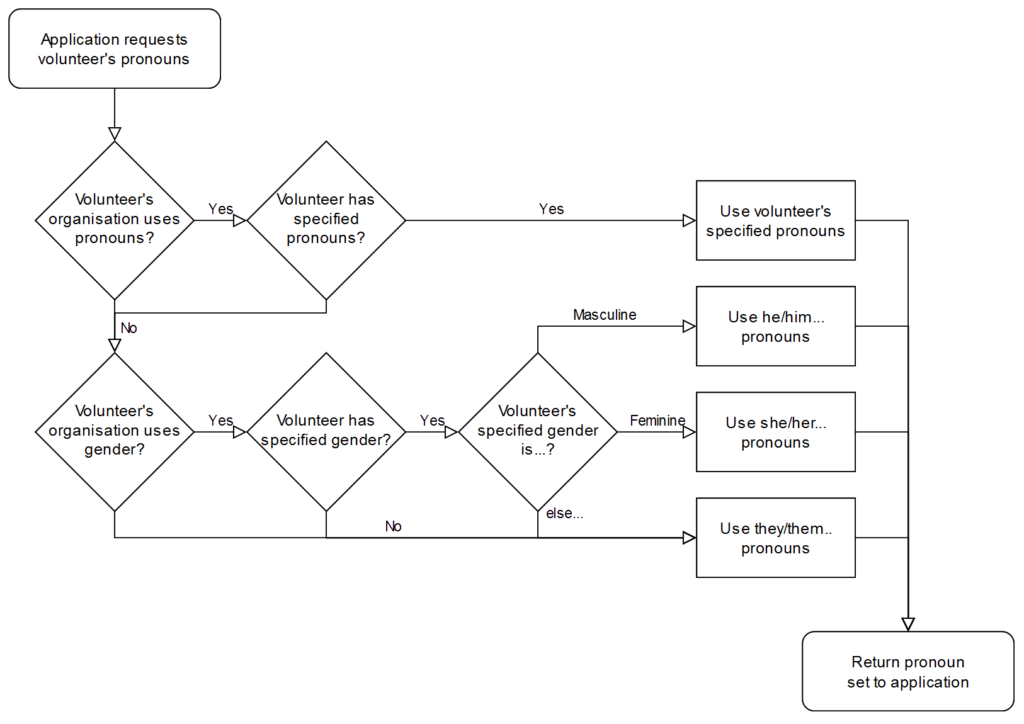
Prior to 2018, Three Rings had a relatively simple approach to how it would use pronouns when referring to volunteers.
If the volunteer’s gender was specified as a “masculine” gender (which particular options are available depends on the volunteer’s organisation, but might include “male”, “man”, “cis man”, and “trans man”), the system would use traditional masculine pronouns like “he”, “his”, “him” etc.
If the gender was specified as a “feminine” gender (e.g .”female”, “woman”, “cis women”, “trans woman”) the system would use traditional feminine pronouns like “she”, “hers”, “her” etc.
For any other answer, no specified answer, or an organisation that doesn’t track gender, we’d use singular “they” pronouns. Simple!
 This selection was reflected throughout the system. Three Rings might say:
This selection was reflected throughout the system. Three Rings might say:
- They have done 7 shifts by themselves.
- She verified her email address was hers.
- Would you like to sign him up to this shift?
Unfortunately, this approach didn’t reflect the diversity of personal pronouns nor how they’re applied. It didn’t support volunteer whose gender and pronouns are not conventionally-connected (“I am a woman and I use ‘them/they’ pronouns”), nor did it respect volunteers whose pronouns are not in one of these three sets (“I use ze/zir pronouns”)… a position it took me an embarrassingly long time to fully comprehend.
So we took a new approach:
The New Way
From 2018 we allowed organisations to add a “Pronouns” property, allowing volunteers to select from 13 different pronoun sets. If they did so, we’d use it; failing that we’d continue to assume based on gender if it was available, or else use the singular “they”.
Let’s take a quick linguistics break
Three Rings‘ pronoun field always shows five personal pronouns, separated by slashes, because you can’t necessarily derive one from another. That’s one for each of five types:
- the subject, used when the person you’re talking about is primary argument to a verb (“he called”),
- object, for when the person you’re talking about is the secondary argument to a transitive verb (“he called her“),
- dependent possessive, for talking about a noun that belongs to a person (“this is their shift”),
- independent possessive, for talking about something that belongs to a person potentially would an explicit noun (“this is theirs“), and the
- reflexive (and intensive), two types which are generally the same in English, used mostly in Three Rings when a person is both the subject and indeirect of a verb (“she signed herself up to a shift”).
Let’s see what those look like – here are the 13 pronoun sets supported by Three Rings at the time of writing:
| Subject | Object | Possessive | Reflexive/intensive | |
| Dependent | Independent | |||
| he | him | his | himself | |
| she | her | hers | herself | |
| they | them | their | theirs | themselves |
| e | em | eir | eirs | emself |
| ey | eirself | |||
| hou | hee | hy | hine | hyself |
| hu | hum | hus | humself | |
| ne | nem | nir | nirs | nemself |
| per | pers | perself | ||
| thon | thons | thonself | ||
| ve | ver | vis | verself | |
| xe | xem | xyr | xyrs | xemself |
| ze | zir | zirs | zemself | |
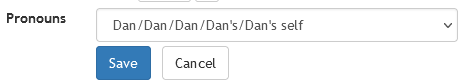
That’s all data-driven rather than hard-coded, by the way, so adding additional pronoun sets is very easy for our developers. In fact, it’s even possible for us to apply an additional “override” on an individual, case-by-case basis: all we need to do is specify the five requisite personal pronouns, separated by slashes, and Three Rings understands how to use them.
Writing code that respects pronouns
Behind the scenes, the developers use a (binary-gendered, for simplicity) convenience function to produce output, and the system corrects for the pronouns appropriate to the volunteer in question:
<%= @volunteer.his_her.capitalize %> account has been created for <%= @volunteer.him_her %> so <%= @volunteer.he_she %> can now log in.
The code above will, dependent on the pronouns specified for the volunteer @volunteer, output something like:
- His account has been created for him so he can now log in.
- Her account has been created for her so she can now log in.
- Their account has been created for them so they can now log in.
- Eir account has been created for em so ey can now log in.
- Etc.
We’ve got extended functions to automatically detect cases where the use of second person pronouns might be required (“Your account has been created for you so you can now log in.”) as well as to help us handle the fact that we say “they are” but “he/she/ey/ze/etc. is“.
It’s all pretty magical and “just works” from a developer’s perspective. I’m sure most of our volunteer developers don’t think about the impact of pronouns at all when they code; they just get on with it.
Is that a complete solution?
Does this go far enough? Possibly not. This week, one of our customers contacted us to ask:
Is there any way to give the option to input your own pronouns? I ask as some people go by she/them or he/them and this option is not included…
You can probably see what’s happened here: some organisations have taken our pronouns property – which exists primarily to teach the system itself how to talk about volunteers – and are using it to facilitate their volunteers telling one another what their pronouns are.
What’s the difference? Well:
When a human discloses that their pronouns are “she/they” to another human, they’re saying “You can refer to me using either traditional feminine pronouns (she/her/hers etc.) or the epicene singular ‘they’ (they/their/theirs etc.)”.
But if you told Three Rings your pronouns were “she/her/their/theirs/themselves”, it would end up using a mixture of the two, even in the same sentence! Consider:
- She has done 7 shifts by themselves.
- She verified her email address was theirs.
That’s some pretty clunky English right there! Mixing pronoun sets for the same person within a sentence is especially ugly, but even mixing them within the same page can cause confusion. We can’t trivially meet this customer’s request simply by adding new pronoun sets which mix things up a bit! We need to get smarter.
A Newer Way?
Ultimately, we’re probably going to need to differentiate between a more-rigid “what pronouns should Three Rings use when talking about you” and a more-flexible, perhaps optional “what pronouns should other humans use for you”? Alternatively, maybe we could allow people to select multiple pronoun sets to display but Three Rings would only use one of them (at least, one of them at a time!): “which of the following sets of pronouns do you use: select as many as apply”?
Even after this, there’ll always be more work to do.
For instance: I’ve met at least one person who uses no pronouns! By this, they actually mean they use no third-person personal pronouns (if they actually used no pronouns they wouldn’t say “I”, “me”, “my”, “mine” or “myself” and wouldn’t want others to say “you”, “your”, “yours” and “yourself” to them)! Semantics aside… for these people Three Rings should use the person’s name rather than a pronoun.
Maybe we can get there one day.
But so long as Three Rings continues to remain ahead of the curve in its respect for and understanding of pronoun use then I’ll be happy.
Our mission is to focus on volunteers and make volunteering easier. At the heart of that mission is treating volunteers with respect. Making sure our system embraces the diversity of the 65,000+ volunteers who use it by using pronouns correctly might be a small part of that, but it’s a part of it, and I for one am glad we make the effort.
Dan Q performed maintenance for GC9EXXC Shady Seat on The Green
This checkin to GC9EXXC Shady Seat on The Green reflects a geocaching.com log entry. See more of Dan's cache logs.
I was out on a head-clearing walk anyway this evening as I waited for my computer to catch up with me on some batch processing work, so I figured I’d check on this cache, which got a DNF earlier today. The cache is in its usual place and is healthy and ready to find… but the colours of some parts of the cache container might trick the eye when seen alongside all the recently fallen autumn leaves…
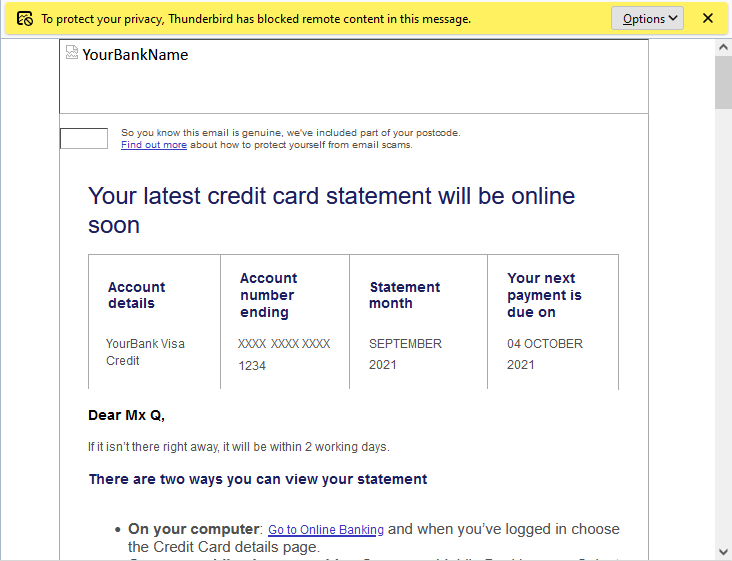
Email Tracking and Paperless Banking
A few weeks ago, my credit card provider wrote to me to tell me that they were switching me back from paperless to postal billing because I’d “not been receiving their emails”.
This came as a surprise to me because I have been receiving their emails. Why would they think that I hadn’t?
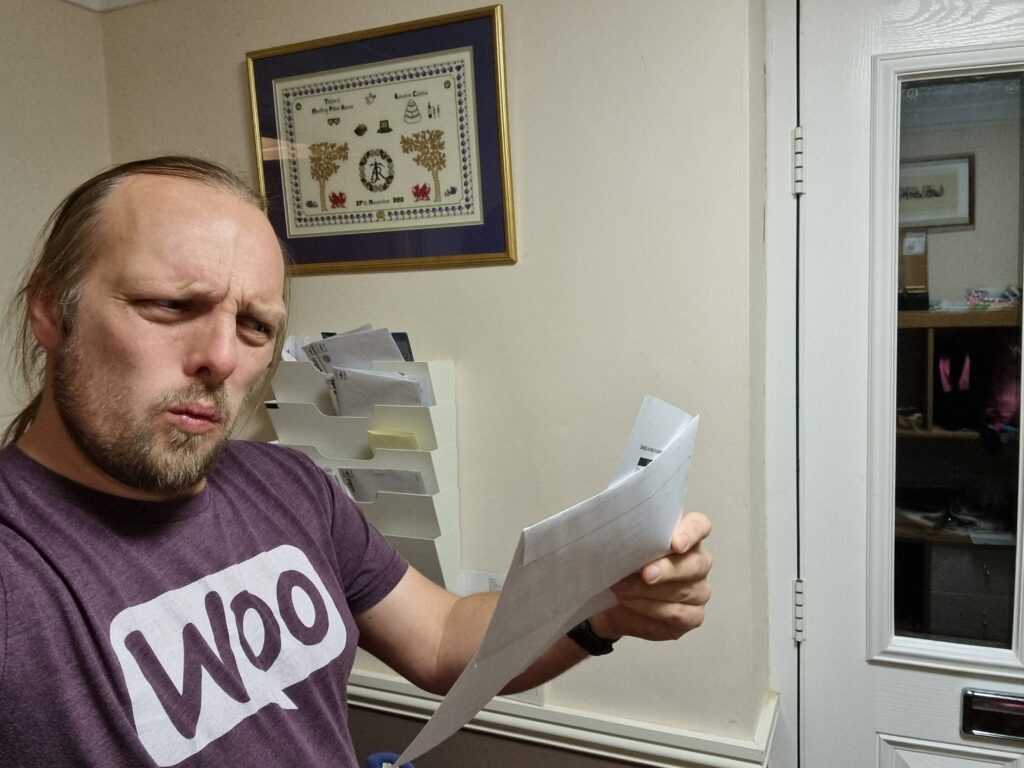
Turns out they have a tracking pixel in their email to track that it’s been opened, as well as potentially additional data such as when it was opened (or re-opened), what email client or clients the recipient uses, what IP address or addresses they read their mail from, and so on.
Naturally, because I don’t like creepy companies tracking what I do on my own computers and try to minimise how much they can do so, I read most of my mail with remote content disabled:
Jeremy just had something to say on this topic, too, based on his recent reading of Design for Safety by Eva PenzeyMoog:
Do you have numbers on how many people opened a particular newsletter? Do you have numbers on how many people clicked a particular link?
You can call it data, or stats, or analytics, but make no mistake, that’s tracking.
Follow-on question: do you honestly think that everyone who opens a newsletter or clicks on a link in a newsletter has given their informed constent to be tracked by you?
Needless to say, I had words with my credit card provider. Paperless billing is useful to almost everybody but it’s incredibly useful for blind and partially-sighted users (who are also the ones least-likely to have images loading in the first place, for obvious reasons) because your computer can read your communication to you which is much more-convenient than a letter. Imagine how annoyed you’d be if your bank wrote you a letter (which you couldn’t read but had to get somebody else to read to you) to tell you that because you don’t look at the images in their emails they’re not going to send them to you any more?
Even if you can somehow justify using tracking technologies (which don’t work reliably) to make general, statistical decisions (“fewer people open our emails when the subject contains the word ‘overdraft’!”), you can’t make individual decisions based on them. That’s just wrong.