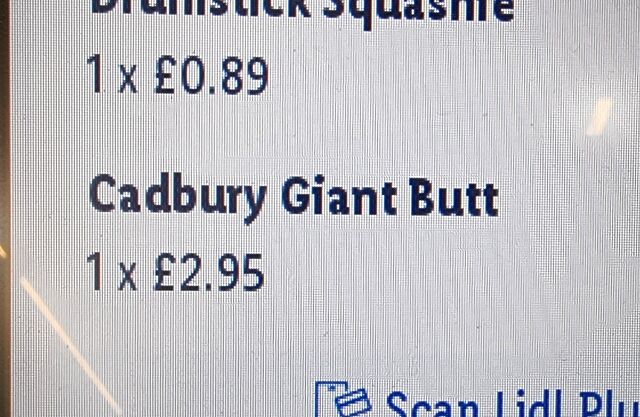
Even this self-checkout thinks I’m eating too much chocolate.
Category: Personal
Geohashing expedition 2026-05-06 51 -1
This checkin to geohash 2026-05-06 51 -1 reflects a geohashing expedition. See more of Dan's hash logs.
Location
Large field near Tawny’s Farm, East of Stanton Harcourt.
Participants
Plans
Between dropping the kids off at school and going to the dentist I had a small window of time in the vicinity of this hashpoint. Could I make it? I figured I’d rush out there and find out. It’d all depend on whether the field was actively in-use (I’m not gonna go tramping through crops!).
Expedition
I’ve been sort-of distracted from geohashing after my house flooded and I had to evacuate earlier this year, so I’ve not had much opportunity to get out and participate. But today, that changed!

After dropping the kids at their schools I drove to Manor Cottages at 51.746, -1.396 where I knew I’d be able to park, then set off at a jog down the rest of Steadys Lane and onto the permissive footpath beyond. I waved to a solitary walker coming the other way, and pressed on until I was close to the field.

Satellite photography suggested that I wouldn’t be able to enter the field directly, so I hopped a gate into the field West of it and was pleased to discover that neither field was currently cultivated.

The hashpoint turned out to be about 700 metres into the field, and it felt sort of open and exposed to go tramping right across the middle of it, but sure enough that’s where I reached the circle of uncertainty, at 08:53.
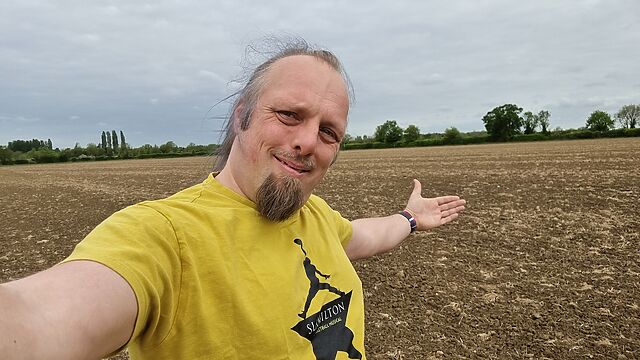

Coming back, I spotted a disused and rusty old gate that provided easier access to the field, which provided a quicker way back to the footpath.

Tracklog
No tracklog today. 😢 I’m not sure if I’ve seen my GPSr since the flood, so I was just working off my my phone.
Four OpenBenches
Despite Google making it harder for me to do so 🤬, I managed to add not one, not two, not three but four new memorial benches to the OpenBenches database during a dog walk this morning.
A particular excitement was adding my first bench with two plaques.
It’s the little things.
A Postcard from Norway!
I got another postcard, and another new country for the senders list.
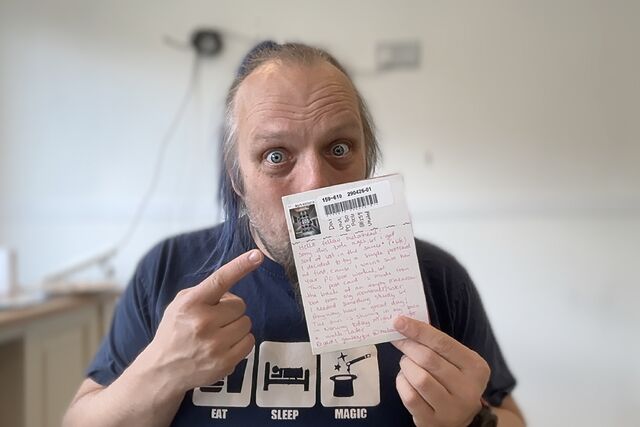
I’ve added it to my gallery. This one’s from grubbyfox, whom I’ve crossed paths with on a Web forum2.
It remains a huge pleasure to receive a postcard from an Internet stranger (or even somebody I already know). It’s so much more tactile, and thoughtful, and human, and real than most of the other feedback I get.3
I guess there’s sort-of a scale of effort that it takes to react to content online. At the lowest end of the scale, barely above “doing nothing”, is “clicking a reaction button” (hey, did you see that you can click one below this?). It takes more effort to fill in a contact form. More still to send an individual email or ping me on Mastodon. But yet more still to write a postcard, find a stamp, go to the postbox… And I really appreciate it when somebody makes the effort.
Footnotes
1 The surprise is dampened only slightly by the fact that my PO Box provider emails me in advance to tell me I’ve received something.
2 Remember Web forums? They’re still very much around, and there are some cool communities if you can find the right one for you.
3 If you want to send my a postcard, my PO Box address is over here…
Note #29064
Moving a static site from GitHub to Codeberg Pages
Late to the party,1 I finally got around to experimentally moving a GitHub Pages-hosted static site to Codeberg. I wanted a low-risk site to try first, so I moved Beige Buttons, the site hosting my “90s PC turbo button simulator” web component.
Mostly for my own benefit later, here’s the steps I took and the things I learned along the way:
- You can migrate a repository across in about two clicks. Easy!
- Codeberg Pages is deployed from the
pagesbranch. If there’s no build step to the static site, all you need to do is rename themainbranch topages(and probably make it the default branch).2 - The default URL is
https://username.codeberg.page/repository. - You can use a custom domain by adding a
.domainsfile that lists domains; if migrating from GitHub Pages you can just rename yourCNAMEfile to.domains. - You’ll need to tweak your DNS
CNAME,ALIAS(or, worst-case,A/AAAA) record to point at Codeberg Pages.3
Change propogation feels slightly slower than GitHub, but perfectly tolerable.
The one thing that’s causing me trouble is that Codeberg Pages’ CORS headers prevent people from hotlinking the Beige Buttons JS, so there are some projects for which this wouldn’t be a suitable migration (issues are raised). But for most static sites, it’d probably Just Work and seems to be a great alternative.
Footnotes
1 With thanks to Kev for reminding me I’d had this on my list.
2 There are other ways to deploy but they don’t support custom domains yet.
3 Like GitHub Pages, Codeberg Pages uses LetsEncrypt for certificate provision, so you don’t need to change any CAA records.
Reply to: Who knows that you blog?
This is a reply to a post published elsewhere. Its content might be duplicated as a traditional comment at the original source.
This one’s been doing the rounds recently, and I’ve enjoyed seeing responses from RNotte, Kev, Alex, and others (there’s a longer list on David’s post).
I feel like my answer is different from those of many other participants: I’ve traditionally made no effort to keep my cyberspace and meatspace separate: probably everybody in my “offline” day-to-day life knows that I write here, and my “online” identity centres around the same central point too.
But lately, I’ve leaned harder on talking about it online. Most of my real-world friends had blogs at some point, but virtually all of those have also long-ago abandoned them1, and along with that shift has come a disinterest in blogging and what it is (or can be) as well. Based on WhatsApp groups we share, most are happier reposting Facebook memes than sharing their own original thoughts in any kind of public forum.
(That said, it made my day when my friend Ele commented a couple of months ago. Hi, Ele!)
Anyway: I think that few would disagree that within popular culture, blogging has “had it’s day”. That’s not to say that there aren’t a great (and growing!) number of blogs out there: just that it’s not the popular touchstone that it was twenty years ago: data-harvesting social media silos have tragically become the “norm”, and for a blogger whose interest was targetting a specific audience… they need to go where the audience went.
Which I guess is something Kev was adjacent to when he said:
I tend to say “I enjoy writing” rather than “I have a blog.” And I think that’s because of the negative connotations blogging has with the general public.
I think some people tend to put “bloggers” in the same bucket as influencers, or podcasters. Which isn’t the case – many of us bloggers have no aspirations of influencing anything, we just like to share out thoughts on a medium we control.
This is the essence of it, I think. Blogging began as a way for people to write about… whatever they liked. But before long it also became a vehicle for marketing: “influencer bloggers” appeared and, let’s face it, made a bad name of it by making the popular expectation be that blogging is something you would do to make a living, rather than for the love of it. I’m not entirely surprised that so many people dropped blogging as a hobby rather than be clumped-in with them.2
But those same people had to jump platforms when social media silos became “the way” to advertise to a large audience, so now they’re all on Instagram, TikTok, and the like. The real personal bloggers – the ones who do it because blogging itself is the right medium for what they want to do – are still here. And, indeed, it feels like they’re in resurgence. Blogs are coming back, baby!3
The question was, though: who do I tell that I blog? And the answer is: absolutely anybody and everybody. But I mostly only make “subscribers” (a term I don’t terribly-much like, because it feels like it implies that increasing that number is some kind of “goal”) out of cyberspace friends, not meatspace friends, these days, I think.
But just sometimes, the worlds collide and somebody I see on the school run will talk about finding something of mine online, or somebody I meet through work will say that they read something I wrote, once. I enjoy these strange organic connections, but it can feel a little weird and awkward to be “recognised” unexpectedly.4
Footnotes
1 I’m pretty sad about it, honestly! I miss seeing blog posts from people I know in “the real world”; I see some, but not many.
2 It’s still a thing, of course, and I get countless requests for paid guest posts, ad placements, participation in link farming, and the like. And I’ve even had people ask me in person how I “monetise” my blog, as if making money from it was ever the goal!
3 Although probably never to the point where people will write about it as an up-and-coming phenomenon in a national newspaper, again. I think we’re past that stage.
4 Unexpected recognition also happens as a result of my work on FreeDeedPoll.org.uk and Three Rings, but these tend to be slightly easier to predict depending on the space I’m in. There are still surprise moments, though, and they’re still sometimes awkward at first!
Spoon bucket
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Wait, this is a real thing?
New life goal unlocked!
The same guy behind these also does buckets of forks. And vlogs about silverware in general.
Everything about that is excellent.
Oh, and happy birthday Jamie, I guess!
Dan Q found GCBMAMH #22 Northmoor Loop
This checkin to GCBMAMH #22 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
For a while I was looking way too high, but in the end I caught a glimpse of this surprisingly well-concealed container.
And that’s the loop complete! Big thanks to the CO for setting this excellent trail spanning so many gorgeous footpaths, many of them new to me despite being relatively local!
Thanks for all the caches, and for a delightful Spring morning’s walk!
Dan Q found GCBMAMC #21 Northmoor Loop
This checkin to GCBMAMC #21 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
A good thematic cache container which we managed to find in a gap between muggle traffic. TFTC.
Dan Q found GCBMAM5 #20 Northmoor Loop
This checkin to GCBMAM5 #20 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
QEF for the geohound and I as we push on into the final straight of our circular walk. TFTC!
Dan Q found GCBMAM2 #19 Northmoor Loop
This checkin to GCBMAM2 #19 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
My GPSr – and my eyes – locked on to a nearby gate post which I searched thoroughly before realising it wasn’t the host: d’oh! Eventually found success while the doggo tried to make more sheepy friends.
Dan Q found GCBMAKZ #18 Northmoor Loop
This checkin to GCBMAKZ #18 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
Solid coordinates walked me right into this one, although I’ve still got to give it credit for excellent camouflage! TFTC.
Dan Q found GCBMAKQ #17 Northmoor Loop
This checkin to GCBMAKQ #17 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
TOTT? Hah! I laugh in the face of your arbitrary requirements. 😂 A little climbing and a big stretch put this cache in my hand with no need for field manufacturing. The dog watched on, bemused, from the path.
Dan Q found GCBMAJB #16 Northmoor Loop
This checkin to GCBMAJB #16 Northmoor Loop reflects a geocaching.com log entry. See more of Dan's cache logs.
It’s funny, I’ve cycled down the nearby back road countless times but never known that this footpath was here.
Near the GZ the geopup saved the day on this one, spotting the requisite geotrail and bringing me back to it. A bit of hair-pulling from the nearby trees didn’t stop me retrieving this nice, large cache. TFTC!