If you’ve received email from Dan, you may have noticed that it’s usually “signed” using a technology called PGP. This digital signature is nearly impossible to forge and helps to prove that the email you’ve received is genuinely from Dan and has not been tampered with by an attacker. You can (and should) verify the signature on your own computer.
The Easy Way
If you’re using an advanced, secure email system like Enigmail (desktop) or Protonmail (web), it’ll probably do this automatically for you. But otherwise, here’s the “for dummies” guide to verifying an email from Dan:
The Hard Way
1. Install prerequisites
Install GPG. On a *nix-like operating system, this might be as simple as e.g. sudo apt install gpg or sudo yum install gpg. On
Windows, installing GPG4Win will give you everything you need.
2. Get Dan’s public key
Import Dan’s public key. You can do this by running e.g. curl https://danq.me/dan_q.gpg.asc | gpg --import (gets the key from this website) or
gpg --receive-key B00A55DAC3F59B517CA3F64F63421D243218A6AC (gets the key from a keyserver): to be extra-safe, do both and compare the results.
3. Extract the message parts to verify
View the raw/original message: it’ll be divided into two parts delineated by a boundary marked by a random string. The first part will contain the message content (including any attachments). The second part will contain a couple of headers and the message signature: the screenshot below illustrates this:
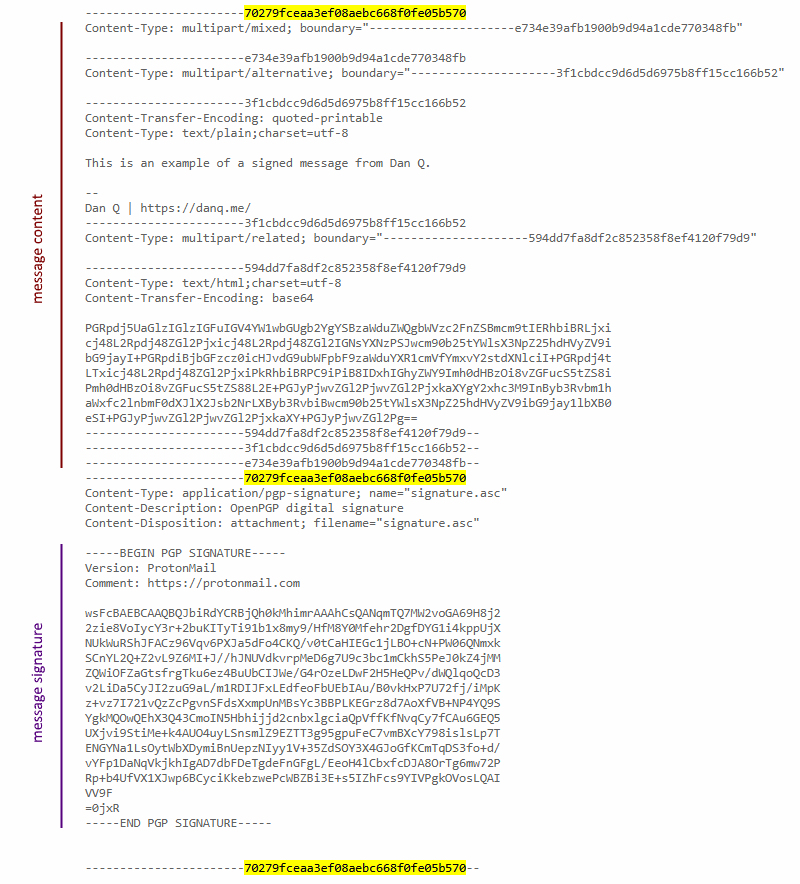
Save/copy-paste the message content into a file and the signature into another; e.g. you might call them “message” and “signature”.
4. Verify the signature
To verify the signature, run:
gpg --verify signature message
(where message and signature are the names of the files you created in step #3)
Other things you can do
Once you’ve got Dan’s public key, you can also use it to send him encrypted messages which can’t be read by anybody who intercepts the email. If you’re interested in learning how to do this, find a good guide online.