Big Rain
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
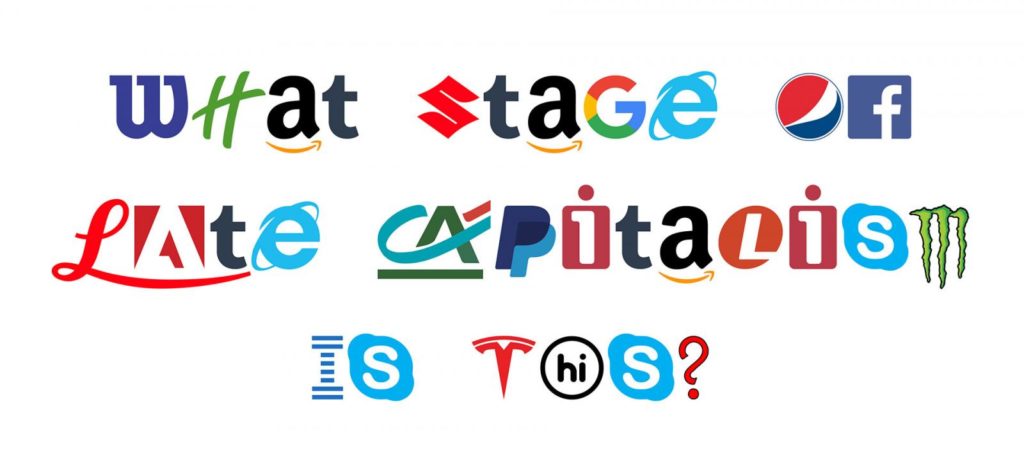
If you’re completely, irrevocably head-over-heels for brands, we finally have just the typeface for you.
Creatives at digital agency Hello Velocity have developed Brand New Roman, a font comprised of 76 corporate brand logos. The Idiocracy-style project is partly parody, but you can actually download the font and use it—and artists have already been playing around with it, too.
Lukas Bentel, partner and creative director at Hello Velocity, tells Muse that the driving idea behind Brand New Roman was simple: “This stage of capitalism is pretty weird. Seems like a good time to spoof it!”
…
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
I’ve generally been pretty defensive of Microsoft Edge, the default web browser in Windows 10. Unlike its much-mocked predecessor Internet Explorer, Edge is fast, clean, modern, and boasts good standards-compliance: all of the things that Internet Explorer infamously failed at! I was genuinely surprised to see Edge fail to gain a significant market share in its first few years: it seemed to me that everyday Windows users installed other browsers (mostly Chrome, which is causing its own problems) specifically because Internet Explorer was so terrible, and that once their default browser was replaced with something moderately-good this would no longer be the case. But that’s not what’s happened. Maybe it’s because Edge’s branding is too-remiscient of its terrible predecessor or maybe just because Windows users have grown culturally-used to the idea that the first thing they should do on a new PC is download a different browser, but whatever the reason, Edge is neglected. And for the most part, I’ve argued, that’s a shame.
But I’ve changed my tune this week after doing some research that demonstrates that a long-standing security issue of Internet Explorer is alive and well in Edge. This particular issue, billed as a “feature” by Microsoft, is deliberately absent from virtually every other web browser.
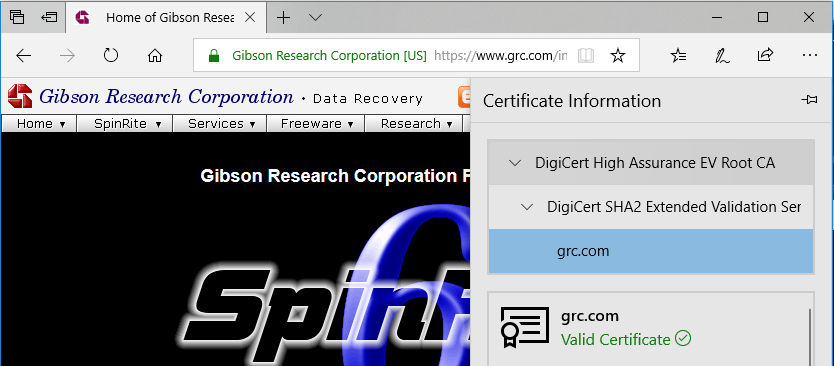
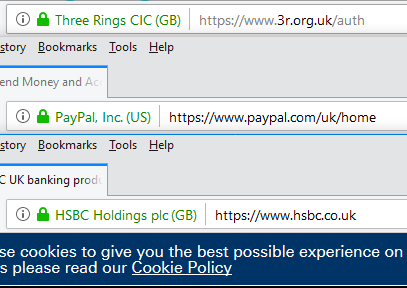
About 5 years ago, Steve Gibson observed a special feature of EV (Extended Validation) SSL certificates used on HTTPS websites: that their extra-special “green bar”/company name feature only appears if the root CA (certificate authority) is among the browser’s default trust store for EV certificate signing. That’s a pretty-cool feature! It means that if you’re on a website where you’d expect to see a “green bar”, like Three Rings, PayPal, or HSBC, then if you don’t see the green bar one day it most-likely means that your connection is being intercepted in the kind of way I described earlier this year, and everything you see or send including passwords and credit card numbers could be at risk. This could be malicious software (or nonmalicious software: some antivirus software breaks EV certificates!) or it could be your friendly local network admin’s middlebox (you trust your IT team, right?), but either way: at least you have a chance of noticing, right?
Browsers requiring that the EV certificate be signed by a one of a trusted list of CAs and not allowing that list to be manipulated (short of recompiling the browser from scratch) is a great feature that – were it properly publicised and supported by good user interface design, which it isn’t – would go a long way to protecting web users from unwanted surveillance by network administrators working for their employers, Internet service providers, and governments. Great! Except Internet Explorer went and fucked it up. As Gibson reported, not only does Internet Explorer ignore the rule of not allowing administrators to override the contents of the trusted list but Microsoft even provides a tool to help them do it!
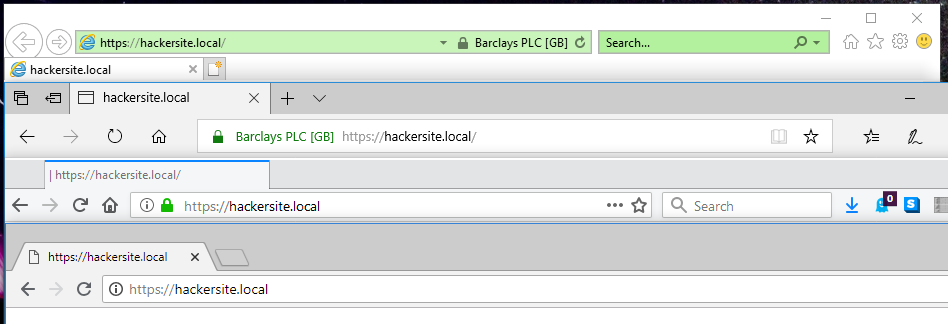
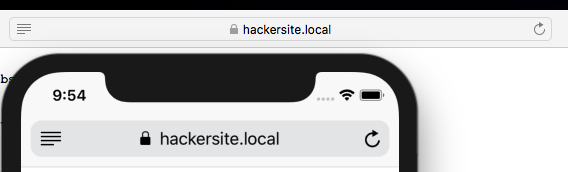
I decided to replicate Gibson’s experiment to confirm his results with today’s browsers: I was also interested to see whether Edge had resolved this problem in Internet Explorer. My full code and configuration can be found here. As is doubtless clear from the title of this post and the screenshot above, Edge failed the test: it exhibits exactly the same troubling behaviour as Internet Explorer.
Thanks, Microsoft.
I shan’t for a moment pretend that our current certification model isn’t without it’s problems – it’s deeply flawed; more on that in a future post – but that doesn’t give anybody an excuse to get away with making it worse. When it became apparent that Internet Explorer was affected by the “feature” described above, we all collectively rolled our eyes because we didn’t expect better of everybody’s least-favourite web browser. But for Edge to inherit this deliberate-fault, despite every other browser (even those that share its certificate store) going in the opposite direction, is just insulting.
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
So Reflex are now designing the 2.0 version of the camera they’ve so far yet to ship version 1.0 of – or even find manufacturing partners for. Add to this the nonsense of trying to build a set of primes, film processor and scanner without securing any more funding and I’m increasingly leaning towards this…
This review of The Glebe Play Park originally appeared on Google Maps. See more reviews by Dan.
Excellent play area especially good for young children. Swings, slides, fort, mini hedge maze, musical instruments, exercise equipment, roundabout, trampoline, and climbing frame make this a well-equipped park, abs it’s kept in good condition. Convenient on-street parking and safe gates to prevent runaways and reassure parents! My little ones (4 and 2) love this compact but rich space.
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Polyamory — having more than one consensual sexual or emotional relationship at once — has in recent years emerged on television, mainstream dating sites like OkCupid and even in research. And experts who have studied these kinds of consensual non-monogomous relationships, say they have unique strengths that anyone can learn from.
Consensual non-monogamy can include polyamory, swinging and other forms of open relationships, according to Terri Conley, an associate professor of psychology at the University of Michigan who has studied consensual non-monogamy. While there aren’t comprehensive statistics about how many people in America have polyamorous relationships, a 2016 study published in the Journal of Sex & Marital Therapy found that one in five people in the U.S. engage in some form of consensual non-monogamy throughout their lives.
But these relationships can still be shrouded in stigma. And people in polyamorous relationships often keep them a secret from friends and family.
…
Really interesting to see quite how-widespread the media appeal is growing of looking at polyamory as more than just a curiosity or something titillating. I’ve long argued that the things that one must learn for a successful polyamorous relationship are lessons that have great value even for people who prefer monogamous ones (I’ve even recommended some of my favourite “how-to” polyamory books to folks seeking to improve their monogamous relationships!), so it pleases me to see a major publication like Time take the same slant.
This month, I shared photos of a mystery box I discovered in a meeting room at work which turned out to be an adapter to a proprietary kind of 13A plug socket and developed a software tool which pixel-scrapes open mapping data to estimate what percentage of a given graticule (degree of latitude by degree of longitude) is covered with water, which could be expected to affect the challenge level for geohashers based in that graticule. This coincided with two consecutive-day geohashing expeditions of my own: one to East Adderbury (with accompanying vlog) where I met some cows and was served an unexpected number of eggs at a pub, and one to the South Downs National Park (with accompanying vlog, and via three geocaches: 1, 2, 3).
I also attended Oxford’s first ever IndieWebCamp and achieved a life goal when my local radio station asked me on-air to stop texting them puns.
Posts marked by an asterisk (*) are referenced by the summary above.
Reposts marked with a dagger (†) include my comments or interpretation.
One off the #bucketlist this morning when local radio station @JACKfmOxford said, on-air, “Dan, please stop texting us puns.”
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
https://www.youtube.com/watch?v=mmrwdTGZxGk
Thanks to the modern electric grid, you have access to electricity whenever you want. But the grid only works when electricity is generated in the same amounts as it is consumed. That said, it’s impossible to get the balance right all the time. So operators make grids more flexible by adding ways to store excess electricity for when production drops or consumption rises.
About 96% of the world’s energy-storage capacity comes in the form of one technology: pumped hydro. Whenever generation exceeds demand, the excess electricity is used to pump water up a dam. When demand exceeds generation, that water is allowed to fall—thanks to gravity—and the potential energy turns turbines to produce electricity.
But pumped-hydro storage requires particular geographies, with access to water and to reservoirs at different altitudes. It’s the reason that about three-quarters of all pumped hydro storage has been built in only 10 countries. The trouble is the world needs to add a lot more energy storage, if we are to continue to add the intermittent solar and wind power necessary to cut our dependence on fossil fuels.
A startup called Energy Vault thinks it has a viable alternative to pumped-hydro: Instead of using water and dams, the startup uses concrete blocks and cranes. It has been operating in stealth mode until today (Aug. 18), when its existence will be announced at Kent Presents, an ideas festival in Connecticut.
…
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Save the dates folks!
On Saturday 22nd September and Sunday 23rd September we will be having the first ever Oxford IndieWebCamp!
It is a free event, but I would ask that you register on Eventbrite, so I can get an idea of numbers.
IndieWebCamp is a weekend gathering of web creators building & sharing their own websites to advance the independent web and empower ourselves and others to take control of our online identities and data.
It is open to all skill levels, from people who want to get started with a web site, through to experienced developers wanting to tackle a specific personal project.
I gave a little presentation about the Indieweb at JS Oxford earlier this year if you want to know more.
Huge thanks to our sponsors for the event, Haybrook IT and White October.
I couldn’t be more excited about this! I really hope that I’m able to attend!
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
Many online accounts allow you to supplement your password with a second form of identification, which can prevent some prevalent attacks. The second factors you can use to identify yourself include authenticator apps on your phone, which generate codes that change every 30 seconds, and security keys, small pieces of hardware similar in size and shape to USB drives. Since innovations that can actually improve the security of your online accounts are rare, there has been a great deal of well-deserved enthusiasm for two-factor authentication (as well as for password managers, which make it easy to use a different random password for every one of your online accounts.) These are technologies more people should be using.
However, in trying to persuade users to adopt second factors, advocates sometimes forget to disclose that all security measures have trade-offs . As second factors reduce the risk of some attacks, they also introduce new risks. One risk is that you could be locked out of your account when you lose your second factor, which may be when you need it the most. Another is that if you expect second factors to protect you from those attacks that they can not prevent, you may become more vulnerable to the those attacks.
Before you require a second factor to login to your accounts, you should understand the risks, have a recovery plan for when you lose your second factor(s), and know the tricks attackers may use to defeat two-factor authentication.
…
A well-examined exploration of some of the risks of employing two-factor authentication in your everyday life. I maintain that it’s still highly-worthwhile and everybody should do so, but it’s important that you know what you need to do in the event that you can’t access your two-factor device (and, ideally, have a backup solution in place): personally, I prefer TOTP (i.e. app-based) 2FA and I share my generation keys between my mobile device, my password safe (I’ll write a blog post about why this is controversial but why I think it’s a good idea anyway!), and in a console application I wrote (because selfdogfooding etc.).
Update: Years later, I’ve finally written a blog post about why keeping 2FA generation keys in your password safe is controversial, and why I do it anyway.
This is a repost promoting content originally published elsewhere. See more things Dan's reposted.
There’s a YouTube video from 2014 simply titled “Batman Suit-up Compilation.” As that description suggests, the 106-second clip, which has received approximately 1.86 million views, is a highlight reel of different times in Batman movies in which the Caped Crusader dons his Batsuit.
It’s a fairly innocuous video, but it’s generated more than 550 comments. And the first responder basically sums up the discussion that continues down the rest of the page: “Was there any point of showing Batman’s ass? Furthermore, why were Bats and Robin wearing codpieces? ”
…
My original plan to divert to the 2018-08-23 51 -1 hashpoint during my planned journey North-to-South along almost the entire length of the 51 -1 graticule was ruined somewhat by the hashpoint turning out be farther North than my starting point! So I changed plans and overshot my destination in order to visit the 50 -1 hashpoint, instead (and find a couple of geocaches on the way). Here’s how that went.
This checkin to geohash 2018-08-23 50 -1 reflects a geohashing expedition. See more of Dan's hash logs.
Hyden Wood, near Chidden. The woods look to be criss-crossed with footpaths, so this might be pretty achievable.
I’d originally planned on heading to 2018-08-23 51 -1 because I anticipated that it’d be on or near my route travelling South along almost the entire length of the 51 -1 graticule, but I didn’t bargain on such a Northerly hashpoint so I’ve changed plans and am now aiming to get to this one some time in the morning (I’m hoping to be in Winchester by lunch).
The full story’s in vlog format, but here’s the summary:
Update: A little research later, it seems that the “ox” in each of Oxford and Droxford have completely different etymological roots! Droxford is derived from an ancient name for the area from some time prior to the Middle Ages: Drocenesforda. “Drocen” means “dry”: the name means “dry ford”. The River Meon, which flows through the area, flows shallow over a chalky bed and is easily forded in many places, as these motorcyclists show. The things you learn!